A SAML 2.0 (Security Assertion Markup Language) is an open standard protocol that enables Single Sign-On that provides authorization and authentication to web-based applications, in this case, Document360.
Supported Identity providers
-
Okta
-
Azure AD (Active Directory)
-
Google
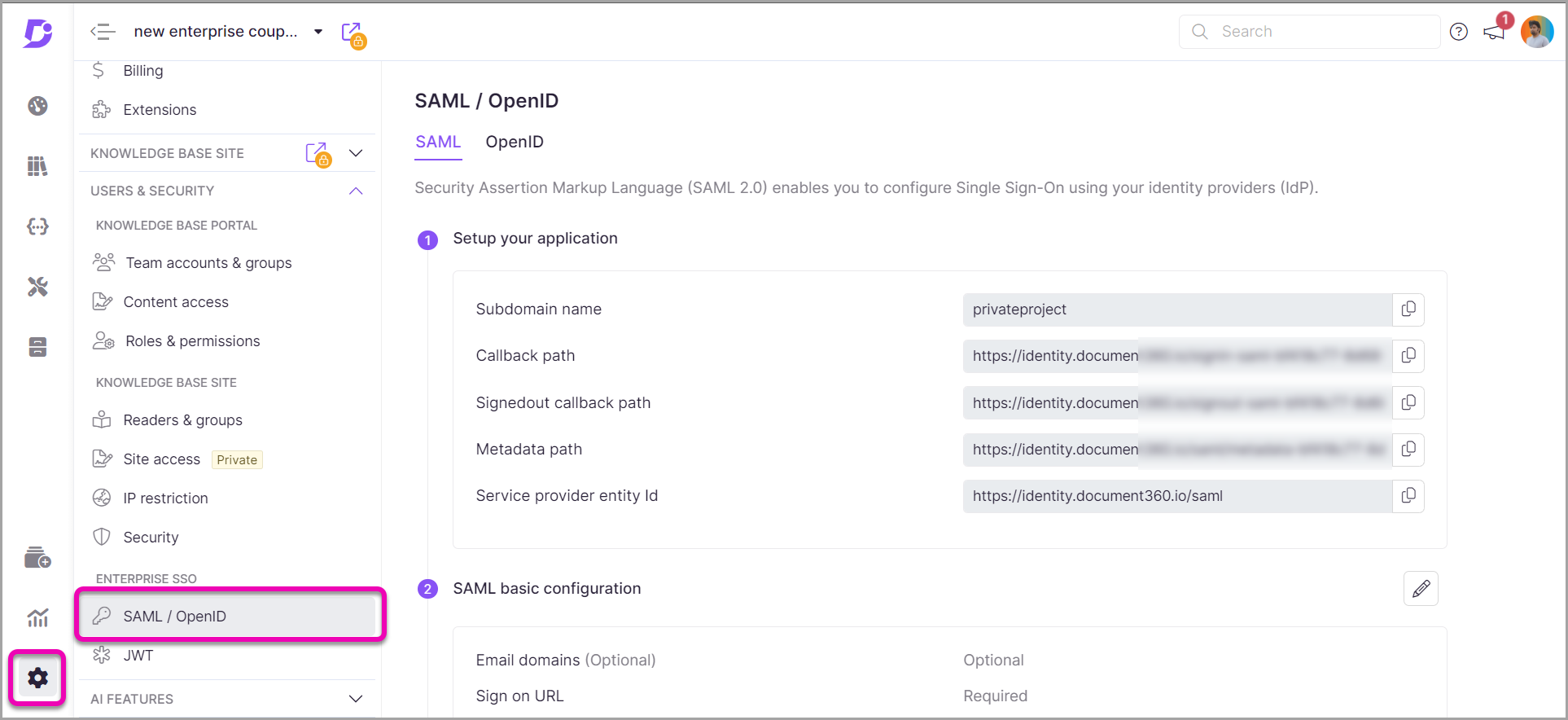
Accessing the SAML SSO page
- Once you've logged in to Document360, choose your intended project
- From the dashboard Settings → Users & Security → SAML/OpenID → SAML
Quick setup using Okta
Follow the setup guides below to get your SAML SSO configured quickly.
- Sign up for Okta, Add an application in Okta, and Create a SAML integration
- Configure the created application on Okta with your Document360 project
- Add or Invite SSO users
- Mapping the same SSO connection in different projects
Once you have successfully configured the SAML SSO with Okta, you can invite members from your project to the configured SSO application.
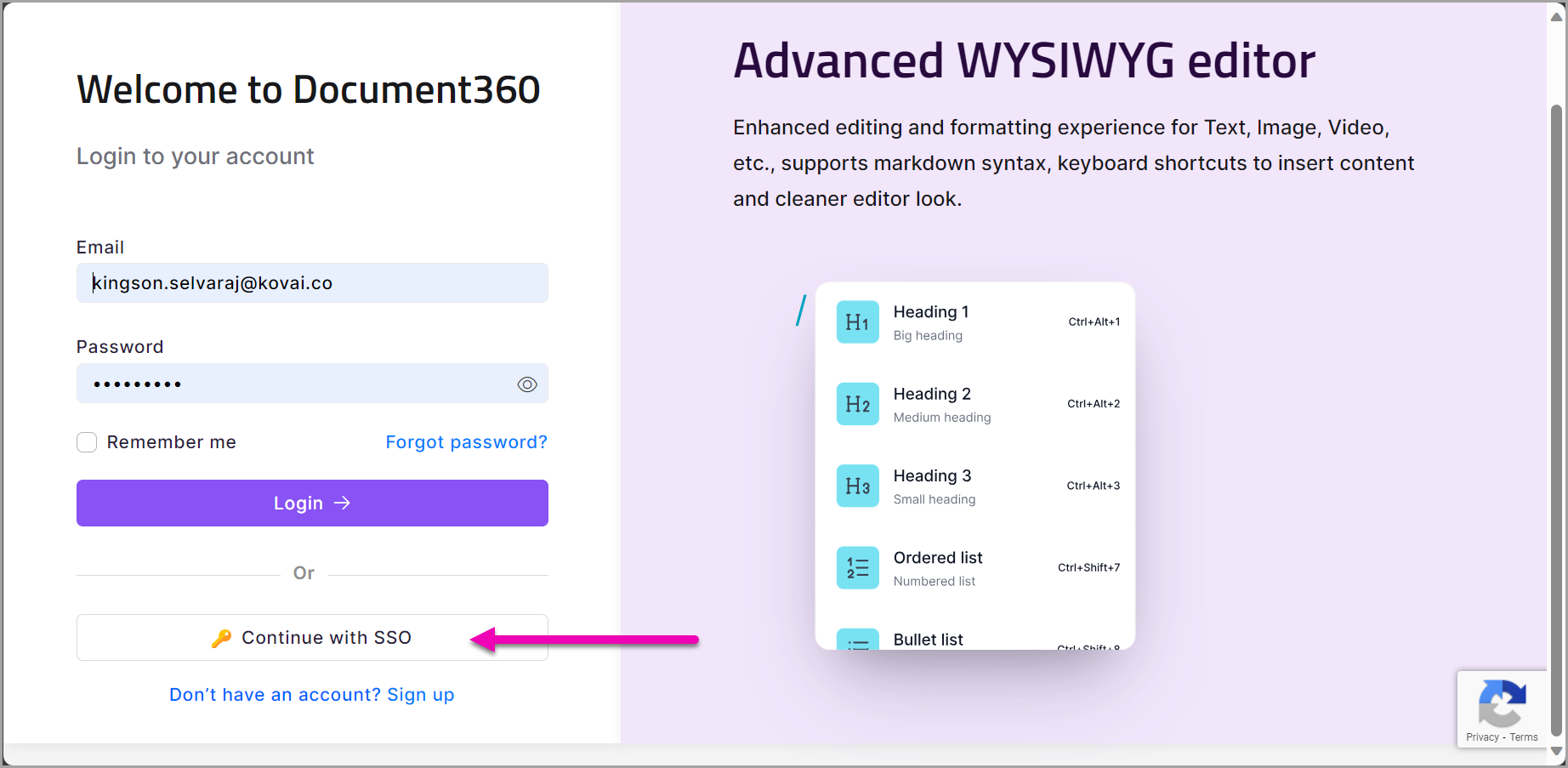
SSO users can log in either as a Document360 or an SSO user. On the initial Login page, click on the SSO option.
Once you click on the SSO option, you are redirected to the SSO user Login page.
Can I add the email domains of different identity providers in the SAML configuration?
All the email domains must be obtained from the same identity provider.