Inicia sesión en tu cuenta de Document360 y selecciona el proyecto para el que deseas configurar el inicio de sesión único de Google SAML con tu cuenta de Google Workspace. A continuación, inicia sesión en tu cuenta de Google Workspace. Si no tienes una cuenta de Google Workspace, puedes crear una en https://workspace.google.com/. Una vez que hayas iniciado sesión en tu cuenta de Google Workplace, accede a la consola de administración usando el botón de Administrador en la parte superior derecha. Ten en cuenta que solo los usuarios con los roles de Propietario o Administrador como Proyecto pueden configurar SSO en Document360.
CONSEJO PROFESIONAL
Se recomienda abrir Document360 y Google Workspace en dos pestañas/ventanas de navegador separadas, ya que configurar SSO en Document360 requerirá cambiar varias veces entre Okta y Document360.
Añadir una aplicación SAML personalizada en Google
En la página principal de la consola de administración, haz clic en la opción Apps y selecciona la opción de aplicaciones SAML .
Haz clic en Añadir aplicación y en el desplegable, selecciona Añadir aplicación SAML personalizada.
En los detalles de la app, introduce cualquier nombre de tu app y haz clic en Continuar.
A continuación, encontrarás la URL SSO, los detalles del ID de la entidad y el Certificado.
Toma nota de estos detalles, ya que los necesitarás al acceder a la página Configurar el Proveedor de Identidad (IdP) en Document360.
En la sección de Certificados, haz clic en el icono de Descargar para guardar el certificado (formato .pem) en el almacenamiento local de tu ordenador.
Tendrás que subir este certificado más adelante en la página Configurar el Proveedor de Identidad (IdP) en Document360.
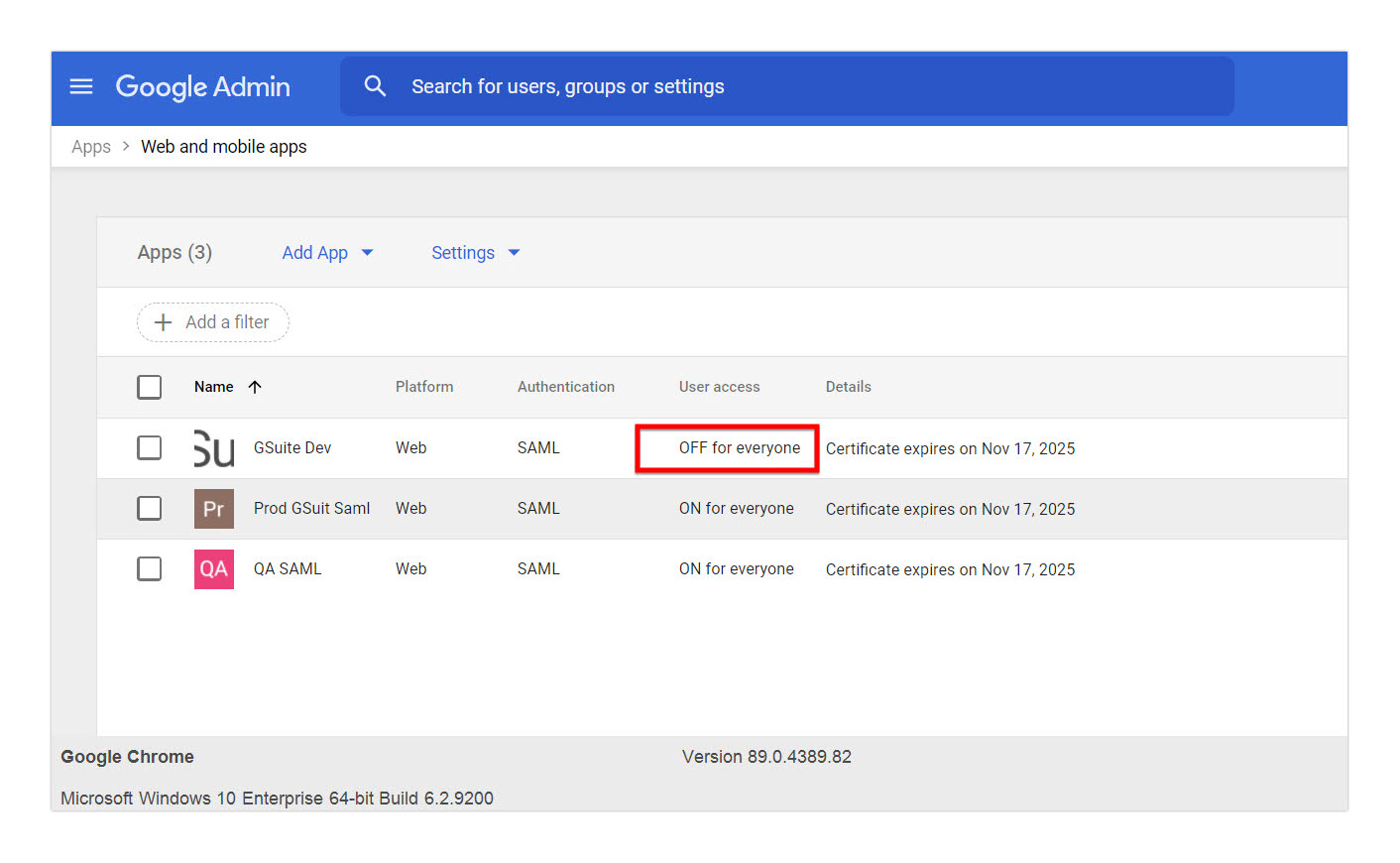
En el acceso de usuario, el estado del servicio será por defecto DESACTIVADO para todos. Debes cambiarlo manualmente a ON para que todos funcionen.
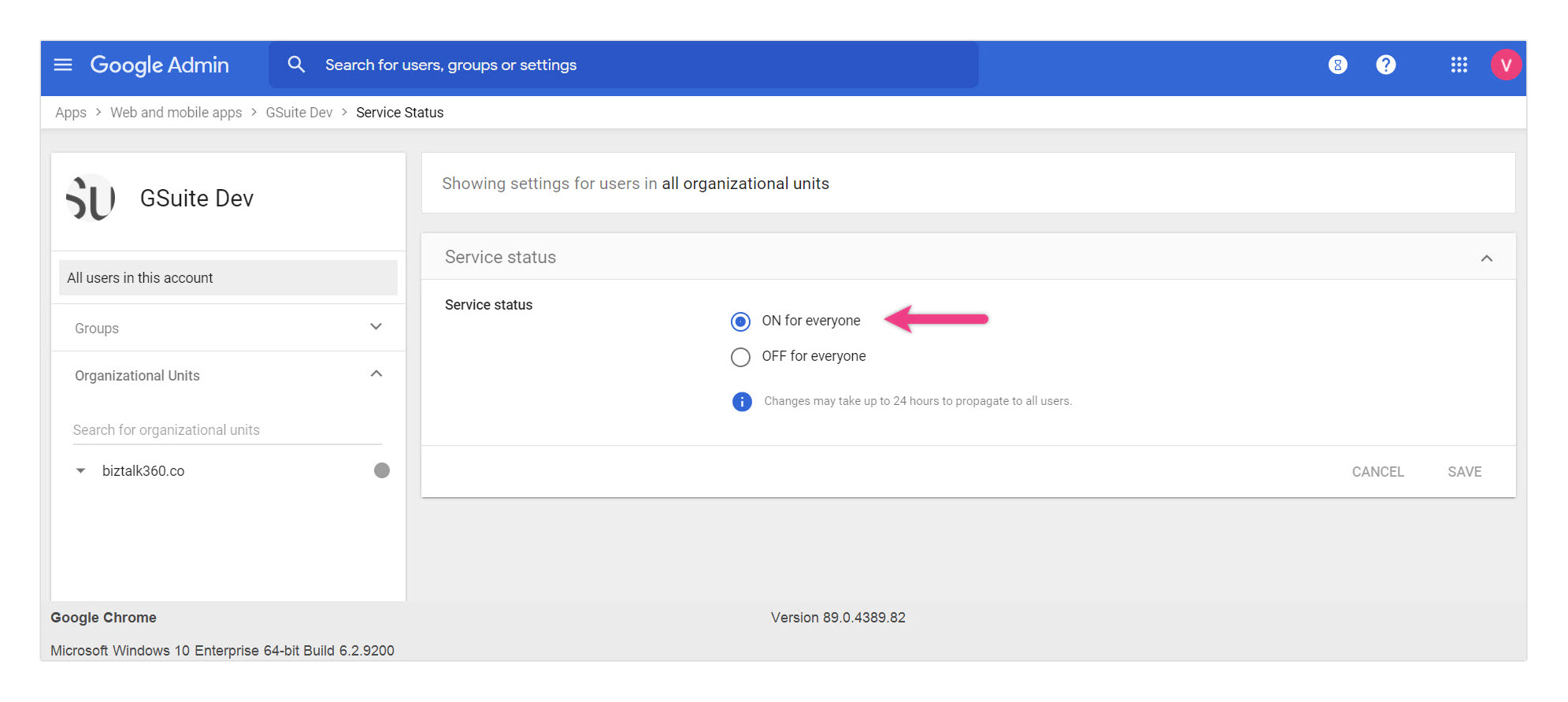
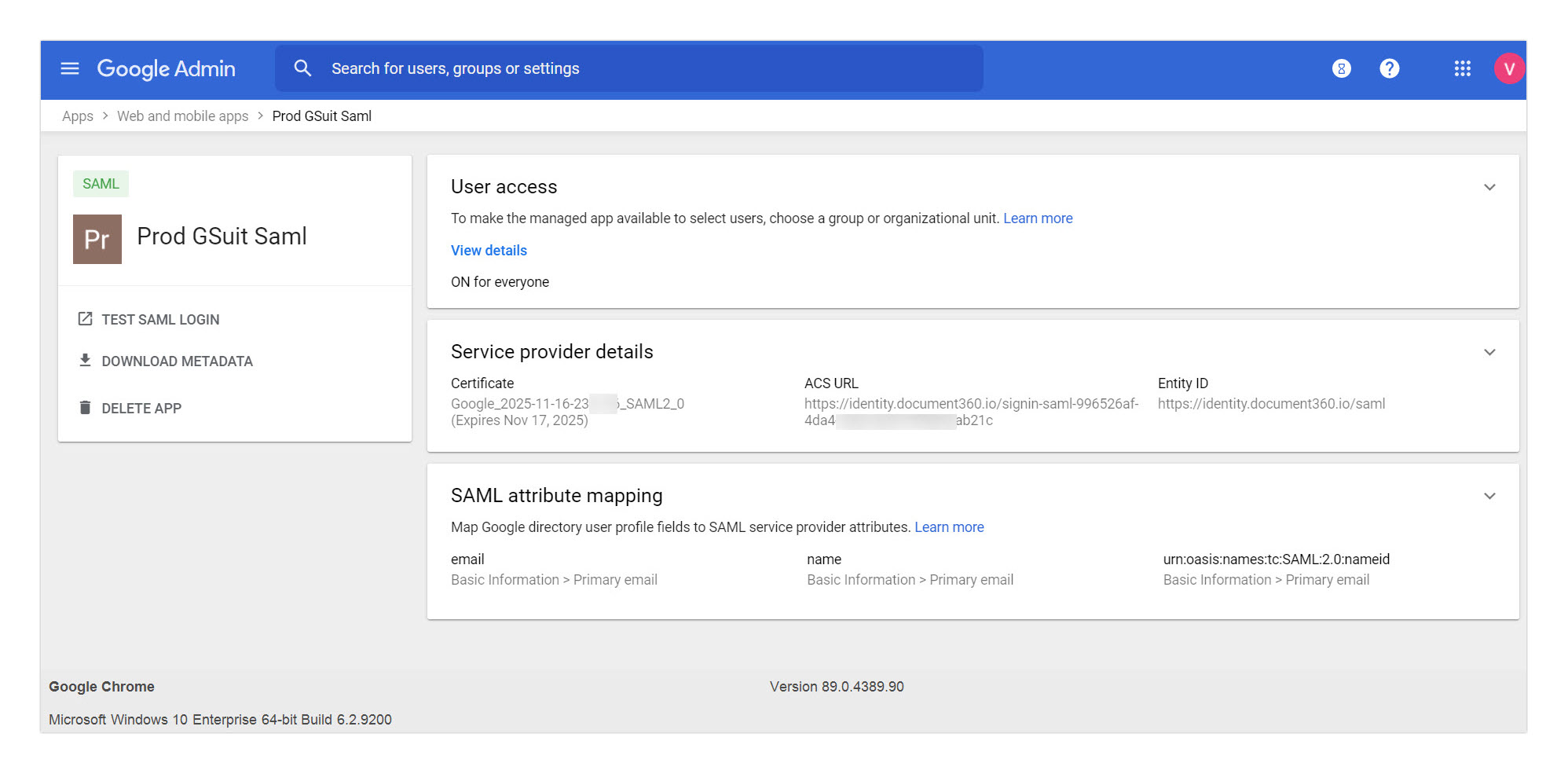
Después de configurarlo en Google, así sería como quedaría tu app SAML.
Configuración del proveedor de servicios
Para configurar el Inicio de Sesión Único (SSO), necesitas detalles del Proveedor de Servicios (SP) como la URL del ACS y el ID de la entidad. Estos detalles estarán disponibles en el panel Crear SSO en Document360. Para acceder al panel de Crear SSO ,
Ve a Configuración > Usuarios y permisos > Configuración SSO.
Haz clic en el botón Crear SSO .
.png)
En la página Elige tu proveedor de identidad (IdP), selecciona Google como proveedor de identidad.
.png)
A continuación, desde la página Configurar el proveedor de servicios (SP ), copie los siguientes parámetros.
Aplicación SAML personalizada de Google | Configuración de Document360 SSO SAML |
|---|---|
ACS URL | Ruta de retrollamada |
ID de entidad | ID de entidad del proveedor de servicios |
.png)
Cambia a la pestaña de Google Workspace y pega los parámetros en la página de la app SAML personalizada de Google.
En formato ID de nombre , selecciona CORREO electrónico en el desplegable
En el ID del nombre selecciona Información básica > correo electrónico principal
Haz clic en el botón Continuar
Atributos
Añade y selecciona campos de usuario en Google Directorio y luego mapéalos a atributos de proveedores de servicios. Añade los siguientes atributos.
Atributos del directorio de Google | Atributos de la aplicación |
|---|---|
Correo electrónico principal | Nombre |
Correo electrónico principal | Correo electrónico |
Correo electrónico principal | urn:oasis:names:tc:SAML:2.0:nameid |
Haz clic en el botón Añadir Mapeado cada vez que añades un atributo y, cuando termines, haz clic en el botón Finalizar .
Configurar el proveedor de identidad (IdP)
Vuelve al panel Document360, a la página Configurar el Proveedor de Servicios (SP ) y haz clic en Siguiente para navegar a la página Configurar el Proveedor de Identidad (IdP ).
El campo Configurar una conexión existente te permite heredar una configuración SSO que ya ha sido creada. Al seleccionar esta opción, la configuración actual de SSO se establecerá como hija y no se podrán hacer cambios.
NOTA
Para más información sobre Herencia, visita Heredar desde otra aplicación.
En la página Configurar el Proveedor de Identidad (IdP), añade la información que anotaste antes desde la página de la app SAML personalizada de Google .
Configuración SSO de Document360 | Información de la aplicación SAML personalizada de Google |
|---|---|
URL de inicio de sesión | SSO URL |
ID de entidad | ID de entidad |
Certificado SAML | Certificado (Sube el archivo .pem reciente que descargaste de Google) |
A continuación, activa o desactiva el interruptor Permitir inicio de sesión IdP según los requisitos de tu proyecto.
.png)
Una vez terminado, haz clic en el botón Siguiente para acceder a la página de aprovisionamiento SCIM .
Provisión SCIM
La provisión SCIM no está soportada cuando Google está configurado como tu Proveedor de Identidad (IdP) en Document360.
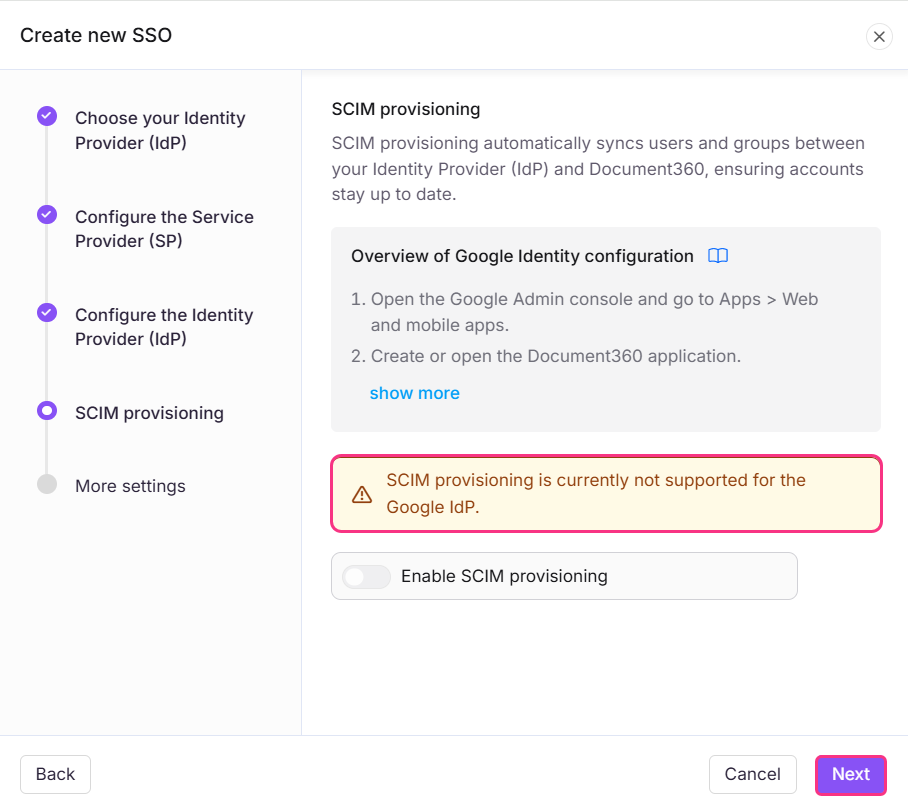
Esta limitación se aplica en dos escenarios:
Al configurar una nueva configuración de Google IdP.
Cuando has heredado una configuración SSO existente que usa Google como IdP.
Haz clic en Siguiente para navegar a Más ajustes.
Más escenarios
En la página de Más configuraciones , introduzca el nombre deseado para la configuración SSO en el campo de nombre SSO .
Introduce el texto que quieres mostrar a los usuarios para el botón de inicio de sesión en el texto del botón Personalizar inicio de sesión.
Activa o desactiva el grupo de lectores de asignación automática y desconecta los interruptores de usuario SSO inactivo según tus necesidades.
Invita a todos tus usuarios o usuarios seleccionados usando los botones de radio Convertir cuentas de usuario y lector existentes a SSO .
.png)
Haz clic en Crear para completar la configuración de la SSO.
La configuración SSO basada en el protocolo SAML se configurará correctamente usando Google .
Heredar de otra aplicación
Al crear una nueva configuración SSO en Document360, puedes heredar la configuración SCIM de una conexión SSO existente. Este enfoque simplifica el proceso de configuración, evita repetir pasos de configuración y ayuda a los administradores a ahorrar tiempo asegurando la coherencia entre integraciones.
Configuración SSO heredada
En la página Configurar Proveedor de Identidad (IdP ), seleccione el campo Configurar una conexión existente y elija la aplicación principal habilitada para SSO SCIM de la que desea heredar. Seleccionar esta opción designará el proyecto actual como proyecto hijo, heredando todas las propiedades relevantes del proyecto padre.
.png)
NOTA
Una vez creada la configuración SSO, los ajustes se heredarán de la aplicación principal y no podrán modificarse en la aplicación hija.
Dado que la provisión SCIM no soporta configuraciones IdP de Google, no se pueden heredar los ajustes SCIM del proyecto principal.
.png)
Mientras que las demás configuraciones de SSO se heredan del proyecto principal, las configuraciones SCIM por sí solas no pueden heredarse.
Gestión de usuarios en Google IdP
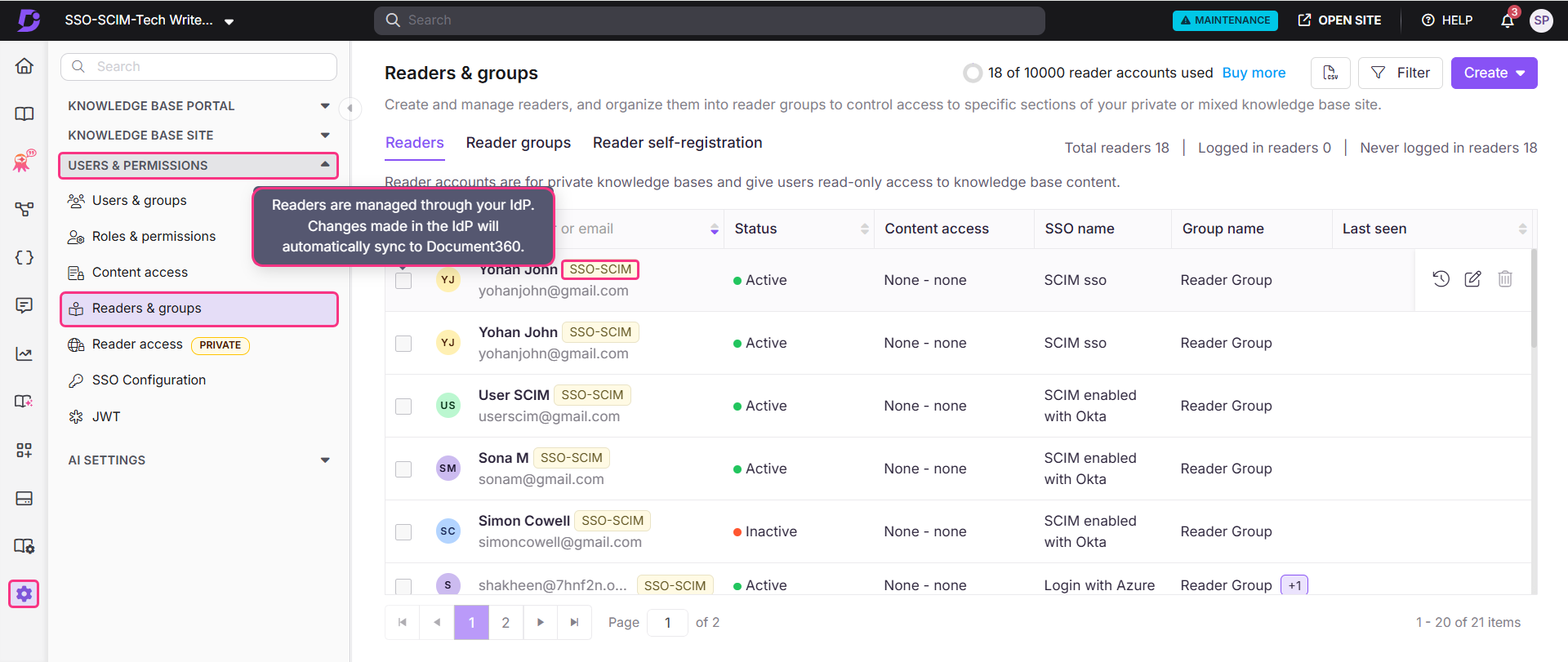
Para ver los lectores añadidos a través de tu aplicación personalizada,
Ve a Document360 y navega a Configuración > Usuarios y permisos > Lectores y grupos.
Selecciona al lector para acceder a su perfil.
Los lectores provisionados mediante SCIM mostrarán una insignia SSO-SCIM junto a su nombre.
NOTA
Cuando SCIM está habilitado, se desactiva editar el nombre de un usuario o eliminar directamente a un usuario en Document360, ya que estas acciones deben gestionarse a través de tu IdP para mantener ambas plataformas sincronizadas. Puedes
solo gestiona el acceso al contenido desde Document360.
Gestionar el acceso al contenido de lectores, usuarios y grupos
El rol de contenido predeterminado asignado a cualquier nuevo usuario, lector o grupo se basa en lo que se configuró durante la configuración del aprovisionamiento SCIM. Los permisos se configurarán como Ninguno por defecto, pero pueden actualizarse en cualquier momento.
Para gestionar el acceso al contenido, selecciona el lector deseado y haz clic en Gestionar el acceso al contenido.
Elige el nivel de acceso deseado en el desplegable y haz clic en Actualizar.
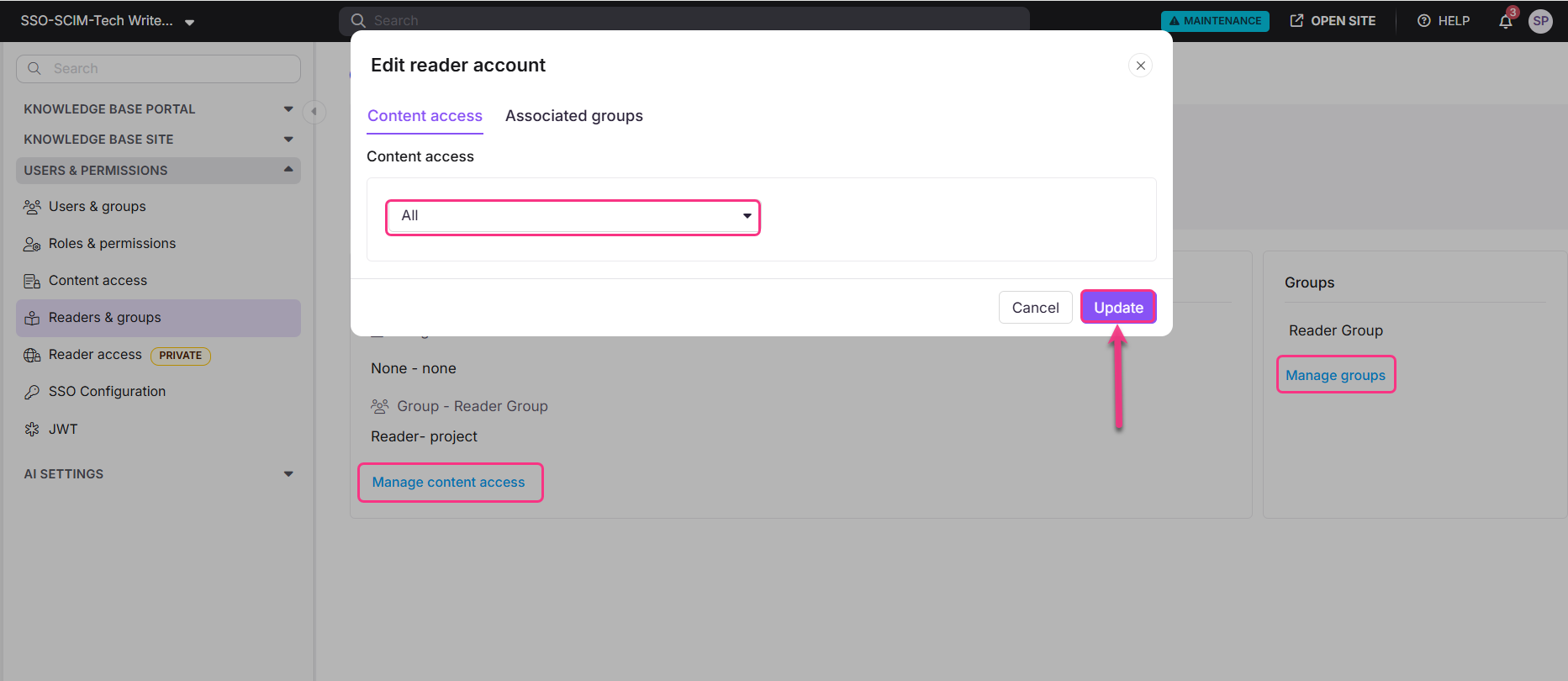
NOTA
También puedes gestionar grupos para un lector haciendo clic en Gestionar grupos en la sección de Grupos de Lectores.