To configure Single Sign-On (SSO) between Document360 and any Identity Provider (IdP) not listed explicitly in Document360, ensure you have the necessary credentials and access to both Document360 and your chosen IdP. Please note that only users with Owner or Admin as Project role can configure SSO in Document360.
PRO TIP
It is recommended to open Document360 and your Identity Provider (IdP) in two separate tabs/browser windows, since configuring SSO in Document360 will require you to switch between Okta and Document360 multiple times.
Adding an Application in your Identity Provider
You must create a new SAML application in your Identity Provider:
Log in to your Identity Provider's admin console using your credentials.
Locate the section where you can create or manage applications (often labeled as Applications, Enterprise Applications, or similar).
Select the option to create a new application.
Configure the basic settings for the new application:
Application Name: Enter a name, e.g., "Document360 SSO".
Application Type: Select SAML 2.0 as the sign-in method.
Save your application settings.
Configuring SAML in your Identity Provider
Next, you will need to configure SAML settings in your Identity Provider using parameters from Document360:
Open Document360 in a separate tab or panel.
Navigate to Settings > Users & permissions > SSO Configuration in Document360.
Click the Create SSO button.
.png)
Select Others as your Identity Provider (IdP) to navigate to the Configure the Service Provider (SP) page automatically.
.png)
In the Configure the Service Provider (SP) page, you'll find the required parameters to configure your SAML integration in the Identity Provider.
In your Identity Provider's SAML configuration, enter the parameters as shown below.
Your IdP | Document360 |
|---|---|
Single Sign-On URL | Callback path |
Entity ID | Service provider entity |
Audience UR | Service provider entity ID or Single Sign-On URL |
.png)
Click Next to navigate to the Configure the Identity Provider (IdP) page.
Attribute Mapping
You may need to configure attribute statements for your Identity Provider:
Attribute Name | Value |
|---|---|
NameID | user.email or user ID |
user.email | |
name | user.name |
Configure these values as required by your Identity Provider.
NOTE
Attribute names are case sensitive.
Feedback and Additional Configuration
Some Identity Providers may ask for feedback or additional information:
Provide any additional configuration details as required by your Identity Provider.
Review your settings and save the SAML configuration.
Document360 SSO Configuration
Finally, complete the SSO configuration in Document360:
Return to the Document360 tab/panel displaying the Configure the Identity Provider (IdP) page.
The Configure an existing connection field allows you to inherit an SSO configuration that has already been created. By selecting this option, the current SSO configuration will be set as the child and no changes can be made to it.
NOTE
For more information on Inheritance, go to Inherit from another application.
Enter the corresponding values from your Identity Provider:
Identity Provider | Document360 |
|---|---|
Single Sign-On URL | Sign-On URL |
Identity Provider Issuer | Entity ID |
SAML Certificate (X.509) | SAML Certificate |
Download the X.509 Certificate from your Identity Provider and upload it to Document360.
Toggle on/off the Allow IdP initiated sign in option based on your project requirements.
.png)
Click Next to proceed to the SCIM provisioning page.
SCIM provisioning
If SCIM is needed,
Turn on the Enable SCIM provisioning toggle.
A confirmation dialog will appear outlining the terms for enabling SCIM. Review the terms, select the checkbox, and click Agree.
.png)
A set of parameters will then be displayed needed to enable SCIM provisioning with your IdP.
.png)
Assign Default role
Turn on the Enable group sync toggle if needed. This automatically assigns users and readers based on your IdP group mappings.
In the Default role field, the role is set to Contributor by default. You can change this from the dropdown if needed.
In the User groups and Reader groups fields, select the groups you want to add. Multiple groups can be added, and they will inherit the default role you selected earlier.
Click Next to navigate to the More Settings page.
More Settings
In the More settings page, configure the following:
SSO name: Enter a name for the SSO configuration.
Customize login button: Enter the text for the login button displayed to users.
Auto assign reader group: This option is only available for existing SSO configurations. For newly created SSO configurations, the Auto assign reader group toggle will not be displayed as SCIM automatically provisions users and groups.
Sign out idle SSO user: Toggle on/off based on your requirements.
Choose whether to invite existing user and reader accounts to SSO.
.png)
Click Create to complete the SSO configuration.
NOTE
When SCIM is enabled, editing a user's name or deleting a user directly in Document360 is disabled, as these actions must be managed through your IdP to keep both platforms in sync. You can only manage the content access from Document360. Deleting a profile in your IdP does not remove it from Document360, the profile will remain with an Inactive status.
The SSO configuration will now be set up in Document360 using your selected Identity Provider.
Inherit from another application
When creating a new SSO configuration in Document360, you can inherit SCIM settings from an existing SSO connection. This approach simplifies the setup process, avoids repeating configuration steps, and helps administrators save time while ensuring consistency across integrations.
Child Inherited SSO configuration
On the Configure Identity Provider (IdP) page, select the Configure an existing connection field and choose the parent SSO SCIM-enabled application you want to inherit from. Selecting this option will designate the current project as the child project, inheriting all relevant properties from the parent.
.png)
NOTE
Once the SSO configuration is created, the SCIM provisioning settings will be inherited from the parent application and cannot be modified in the child application.
Parent Inherited SSO Configuration
The parent application will display a list of all projects that have inherited its configuration. Any changes made to the parent application will automatically be reflected in the child application.
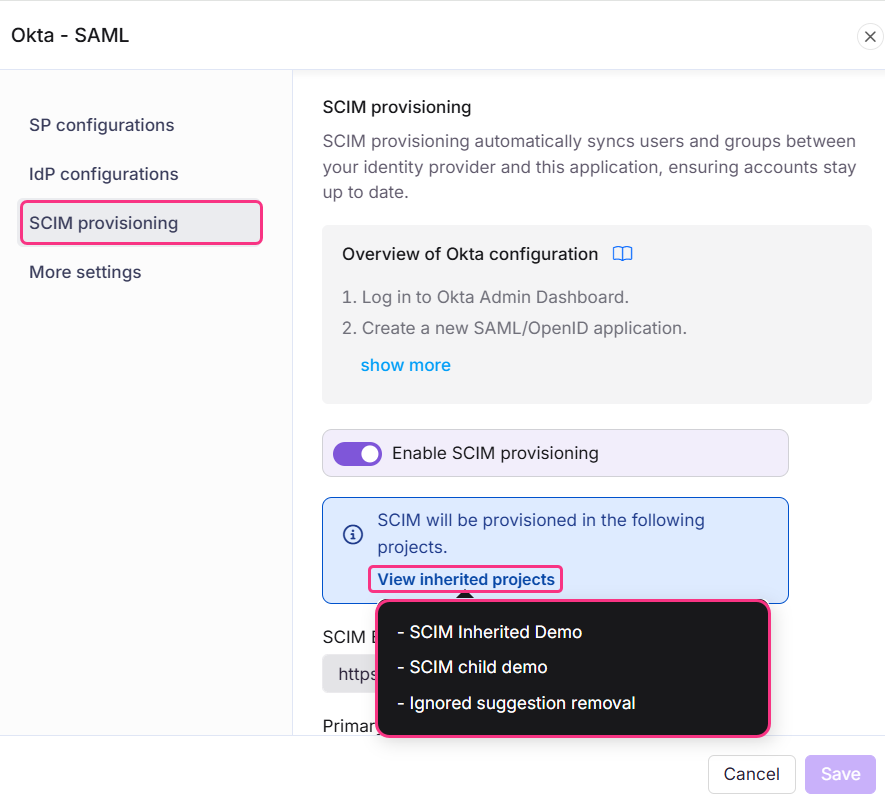
If SCIM is enabled in the parent project after child projects have already inherited it, the users and groups will be automatically provisioned to all child projects in the background.
Enabling inheritance makes it easier to manage multiple SSO configurations with SCIM enabled, as all settings are controlled from one parent application. This saves time and reduces the effort required to manage each configuration individually.