Before setting up Single Sign-On (SSO) between Document360 and Okta using the OpenID protocol, ensure you have administrative access to Okta. Please note that only users with Owner or Admin as Project role can configure SSO in Document360.
PRO TIP
It is recommended to open Document360 and Okta in two separate tabs/browser windows since configuring SSO in Document360 will require you to switch between Okta and Document360 multiple times.
Sign up for Okta
Access to an Okta account is required for configuring SSO with Document360. If you don't have an account:
Navigate to Okta Developer Sign-Up and complete the sign-up process.
Once you log in to Okta with your credentials, you will be navigated to the Okta Admin Console page.
Adding an Application in Okta
To create a Document360 SSO configuration using Okta, follow these steps:
Log in to Okta using your account credentials.
Switch to the admin user role by clicking on Admin at the top right next to your profile name.
From the left navigation list, expand the Applications dropdown and click Applications.
Click the Create App Integration button and select OIDC - OpenID Connect as the Sign-in method.
Choose Web Application as the Application type, then click Next.
On the New Web App Integration page, enter a name for your app in the App integration name field.
.gif)
Document360 Service Provider (SP) Configuration
Next, you will need to configure Okta with the Service Provider (SP) details provided by Document360:
Open Document360 in a separate tab or panel.
Navigate to Settings > Users & permissions > SSO Configuration in Document360.
Click the Create SSO button.
.png)
Select Okta as your identity provider to automatically navigate to the Configure the Service Provider (SP) page.
.png)
In the Configure the Service Provider (SP), select the OpenID radio button to configure SSO with OpenID.
This page will display a set of parameters.
.png)
Go to the New Web App Integration page on Okta, and enter the parameters from Document360 as shown below.
Okta | Document360 |
|---|---|
Sign in redirect URI | Sign-in redirect URIs |
Sign out redirect URI | Sign-out redirect URIs |
.png)
Next, scroll down to Assignments and select a Controlled access by selecting the desired radio button.
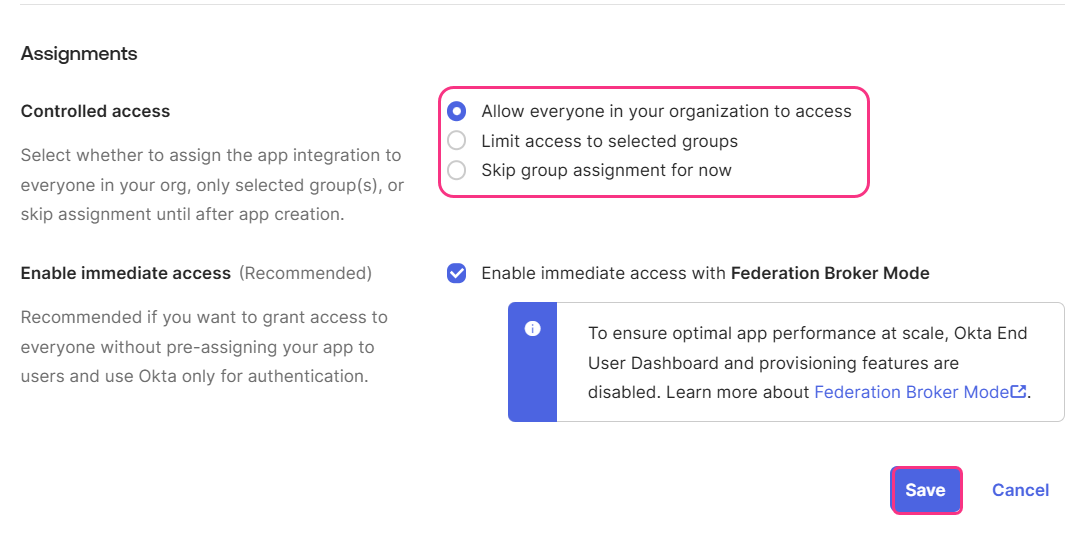
Click Save. You will be redirected to the Application’s General page.
Document360 OpenID SSO Configuration
Now, configure the SSO settings in Document360:
Return to the Document360 tab/panel displaying the Configure the Service Provider (SP) page.
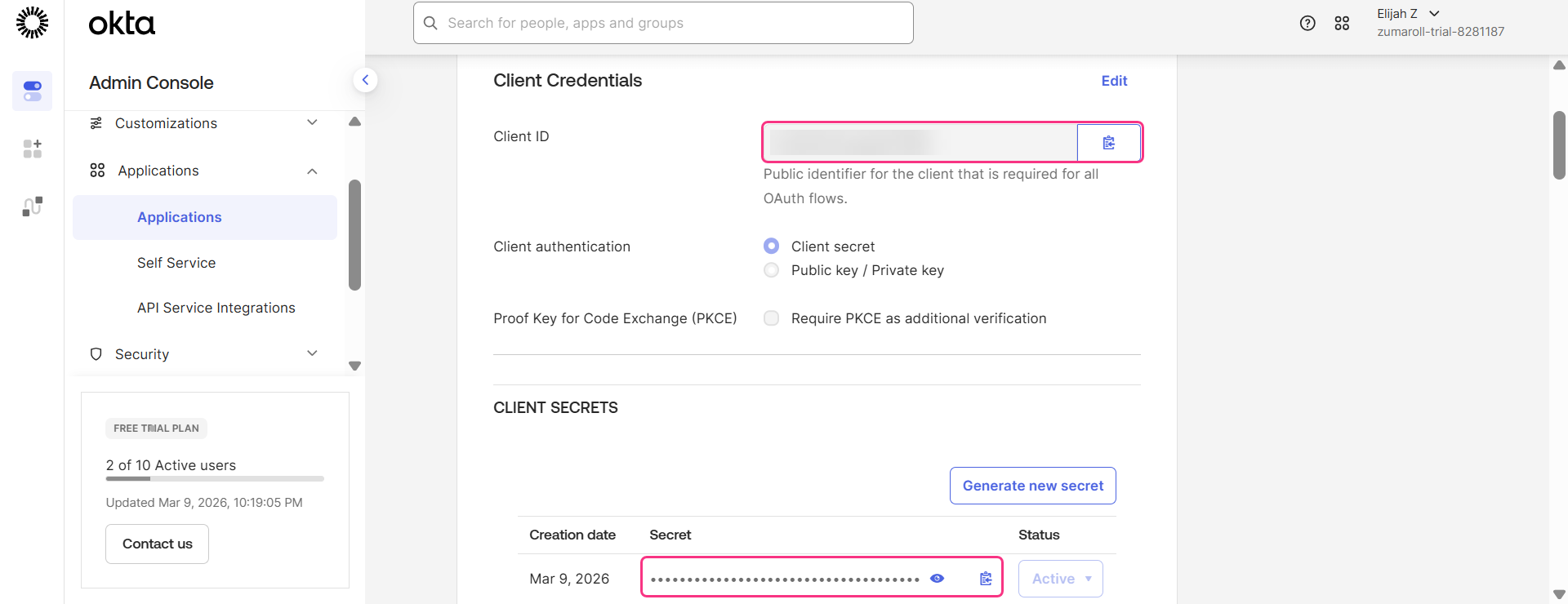
Click Next to navigate to the Configure the Identity Provider (IdP) page and enter the corresponding values from your Okta configuration:
.png)
Okta | Document360 |
|---|---|
Client ID | Client ID |
Client Secret | Client Secret |
Issuer URI | Authority |
NOTE
To find the Issuer URI in Okta, navigate to Security > API.
In the Scope (optional) field, type a scope value and click + to add it as a chip. This defines what user information or permissions Document360 requests from your identity provider.
You can add up to 3 scopes.
Ensure that the Client ID and Client Secret match the values generated in Okta.
Click Next to proceed to the SCIM provisioning page.
SCIM Provisioning
If SCIM is needed,
Turn on the Enable SCIM provisioning toggle. A confirmation dialog will appear, read the terms and click Agree.
The parameters required to complete the SCIM configuration in Okta will then be displayed.
.png)
Go to Okta, expand the Applications dropdown in the left navigation bar, and click Applications.
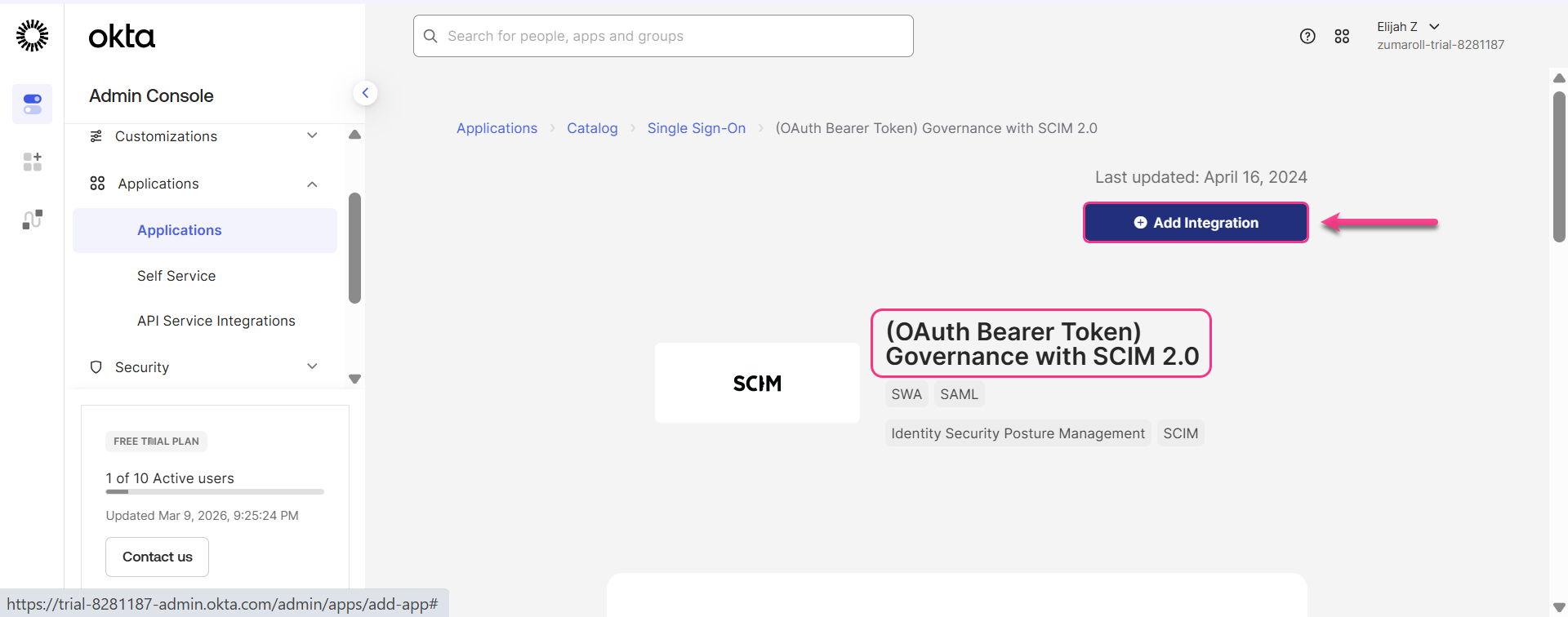
Click Browse App Catalog and search for SCIM 2.0 (OAuth Bearer Token), then select See all results.
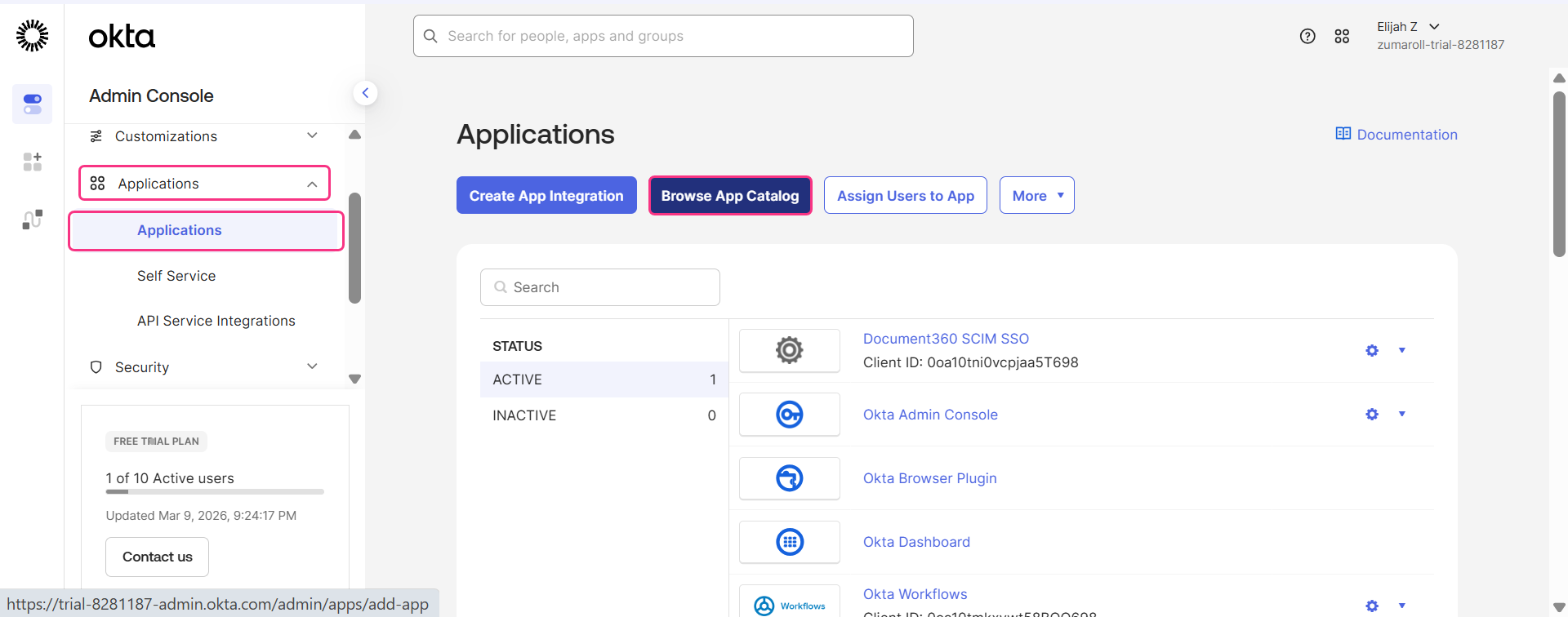
From the search results select (OAuth Bearer Token) Governance with SCIM 2.0 and click Add Integration.
NOTE
Make sure to select the correct App. Do not select the Test app version.
In the General Settings page, you can change your Application label, and click Next.
.png)
Then click Done in the Sign-On options page.
NOTE
Configuration is not needed in this step as we have already configured OpenID in the previous steps. This app is created only for SCIM provisioning.
Navigate to Provisioning tab and select Configure API Integration.
Select the Enable API Integration checkbox and a set of fields will be displayed.
Enter the parameters from Document360 to Okta as shown below.
Okta | Document360 |
|---|---|
Base URL | SCIM Base URL |
OAuth Bearer Token | Primary secret token |
.png)
NOTE
Do not click Test Connector Configuration yet. At this stage, SCIM provisioning will not work with Document360 because the SSO configuration set up is not completed in Document360.
Once you’re done, navigate back to Document360 to complete the configuration.
Assign default role
Turn on the Enable group sync toggle if needed.
In the Default role field, the role is set to Contributor by default. You can change this from the dropdown if needed.
In the User groups and Reader groups fields, select the groups you want to add. Multiple groups can be added, and they will inherit the default role you selected earlier.
Click Next to navigate to the More Settings page.
More Settings
In the More settings page, configure the following:
SSO name: Enter a name for the SSO configuration.
Customize login button: Enter the text for the login button displayed to users.
Auto assign reader group: This option is only available for existing SSO configurations. For newly created SSO configurations, the Auto assign reader group toggle will not be displayed as SCIM automatically provisions users and groups.
Sign out idle SSO user: Toggle on/off based on your requirements.
Choose whether to invite existing user and reader accounts to SSO.
.png)
Click Create to complete the OpenID SSO configuration.
Complete SCIM integration with Okta
To complete SCIM provisioning with Okta,
Navigate back to Okta page.
Click Test API Credentials and a success message should show up, confirming that the created SCIM app is integrated successfully.
.png)
Click Save.
Next, go to Provisioning tab and select To App and click Edit on the Provisioning to App section.
Select the following supported actions only.
Create Users
Update User Attributes
Deactivate Users
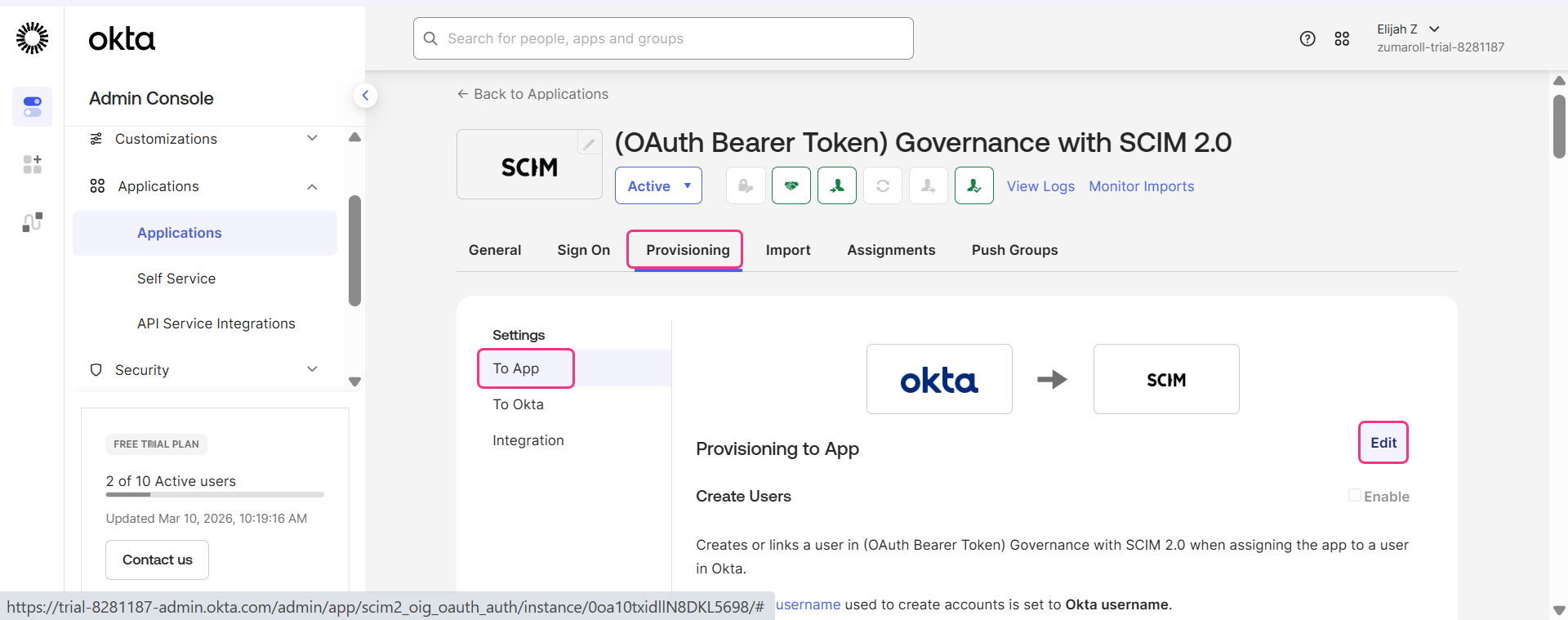
Then click Save.
SCIM Provisioning with Okta OpenID is configured successfully.
The SSO configuration based on the OpenID protocol has been configured using Okta successfully.
NOTE
For more information on how to manage users, readers and groups. Go to Managing Users and Readers with SCIM in Okta.