Before setting up Single Sign-On (SSO) between Document360 and an OpenID Identity Provider (IdP) not explicitly listed in Document360, ensure you have access to both Document360 and your chosen IdP. Please note that only users with Owner or Admin as Project role can configure SSO in Document360.
PRO TIP
It is recommended to open Document360 and the Identity Provider (IdP) in two separate tabs/browser windows, since configuring SSO in Document360 will require you to switch between Okta and Document360 multiple times.
Adding an Application in Your Identity Provider
You'll need to create a new OpenID application in your Identity Provider:
Log in to your Identity Provider's admin console using your credentials.
Navigate to the section where you can create or manage applications (often labeled as Applications, Enterprise Applications, or similar).
Select the option to create a new application.
Set up the basic settings for your new application:
Application Name: Enter a name, e.g., "Document360 OpenID SSO".
Application Type: Select OpenID Connect as the sign-in method.
Save your application settings.
Configuring OpenID in Your Identity Provider
You will need to configure OpenID settings in your Identity Provider using parameters from Document360:
Open Document360 in a separate tab or panel.
Navigate to Settings > Users & permissions > SSO Configuration in Document360.
Click the Create SSO button.
.png)
Select Others as your Identity Provider (IdP) on the Choose your Identity Provider (IdP) page to navigate to the Configure the Service Provider (SP) page in Document360.
.png)
Choose OpenID as the protocol in the Configure the Service Provider (SP) page in Document360.
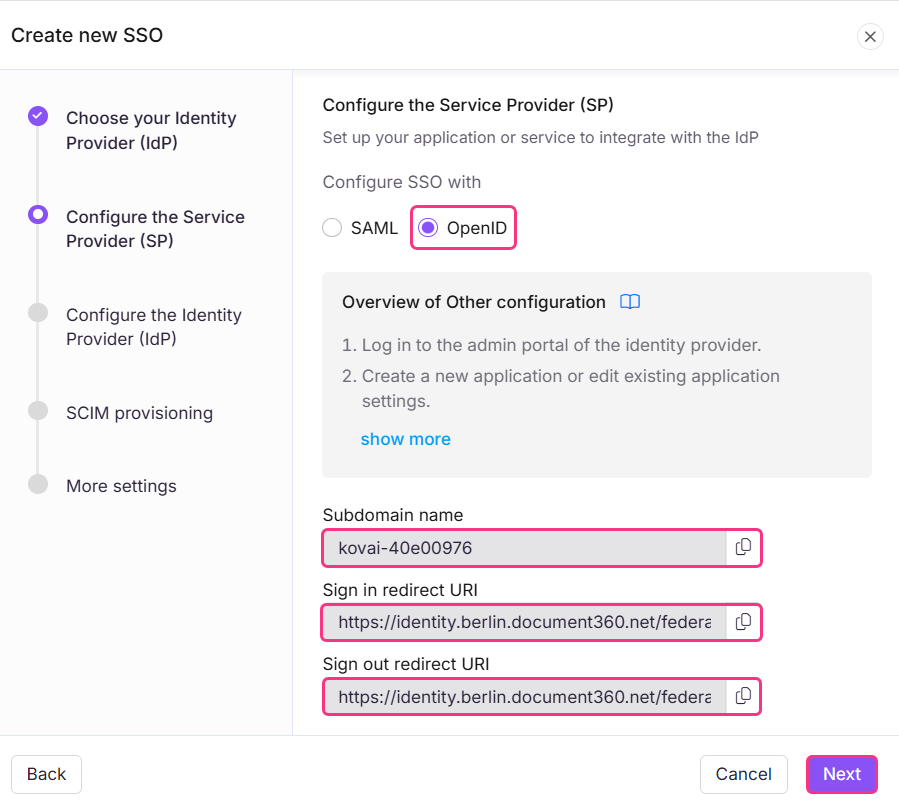
This page will provide the required parameters for configuring OpenID in your Identity Provider. In your Identity Provider's OpenID configuration enter the parameters as shown below.
Your IdP | Document360 |
|---|---|
Subdomain name | Subdomain name |
Redirect URL | Sign in redirect URL |
Redirect URL | Sign out redirect URL |
Scope and Claims
Ensure that the following scopes and claims are included:
Scope | Description |
|---|---|
openid | Required for OpenID authentication |
Access to the user's email | |
profile | Access to the user's basic profile info |
Map the required claims in your Identity Provider:
Claim | Value |
|---|---|
sub | user ID or identifier |
user.email | |
name | user.name |
Review the settings and save your configuration.
Document360 OpenID SSO Configuration
Now, configure the SSO settings in Document360:
Return to the Document360 tab/panel displaying the Configure the Service Provider (SP) page and click Next to navigate to the Configure the Identity Provider (IdP) page.
.png)
The Configure an existing connection field allows you to inherit an SSO configuration that has already been created. By selecting this option, the current SSO configuration will be set as the child and no changes can be made to it.
Enter the parameters from your IdP to Document360 as shown below.
Document360 | Identity provider |
|---|---|
Client ID | Client ID |
Client Secret | Client Secret |
Authority | Authorization URL or Endpoint |
Upload the necessary certificates or keys, if required.
Click Next to proceed to the SCIM provisioning page.
SCIM provisioning
If SCIM is needed,
Turn on the Enable SCIM provisioning toggle.
.png)
A confirmation dialog will appear outlining the terms for enabling SCIM. Review the terms, select the checkbox, and click Agree.
A set of parameters will then be displayed needed to enable SCIM provisioning with your IdP.
.png)
Assign Default role
Turn on the Enable group sync toggle if needed. This automatically assigns users and readers based on your IdP group mappings.
In the Default role field, the role is set to Contributor by default. You can change this from the dropdown if needed.
In the User groups and Reader groups fields, select the groups you want to add. Multiple groups can be added, and they will inherit the default role you selected earlier.
Click Next to navigate to the More Settings page.
More Settings
In the More settings page, configure the following:
SSO name: Enter a name for the SSO configuration.
Customize login button: Enter the text for the login button displayed to users.
Auto assign reader group: This option is only available for existing SSO configurations. For newly created SSO configurations, the Auto assign reader group toggle will not be displayed as SCIM automatically provisions users and groups.
Sign out idle SSO user: Toggle on/off based on your requirements.
Choose whether to invite existing user and reader accounts to SSO.
.png)
Click Create to complete the OpenID SSO configuration.
The SSO configuration will now be set up in Document360 using your selected Identity Provider.
Managing Users in your IdP
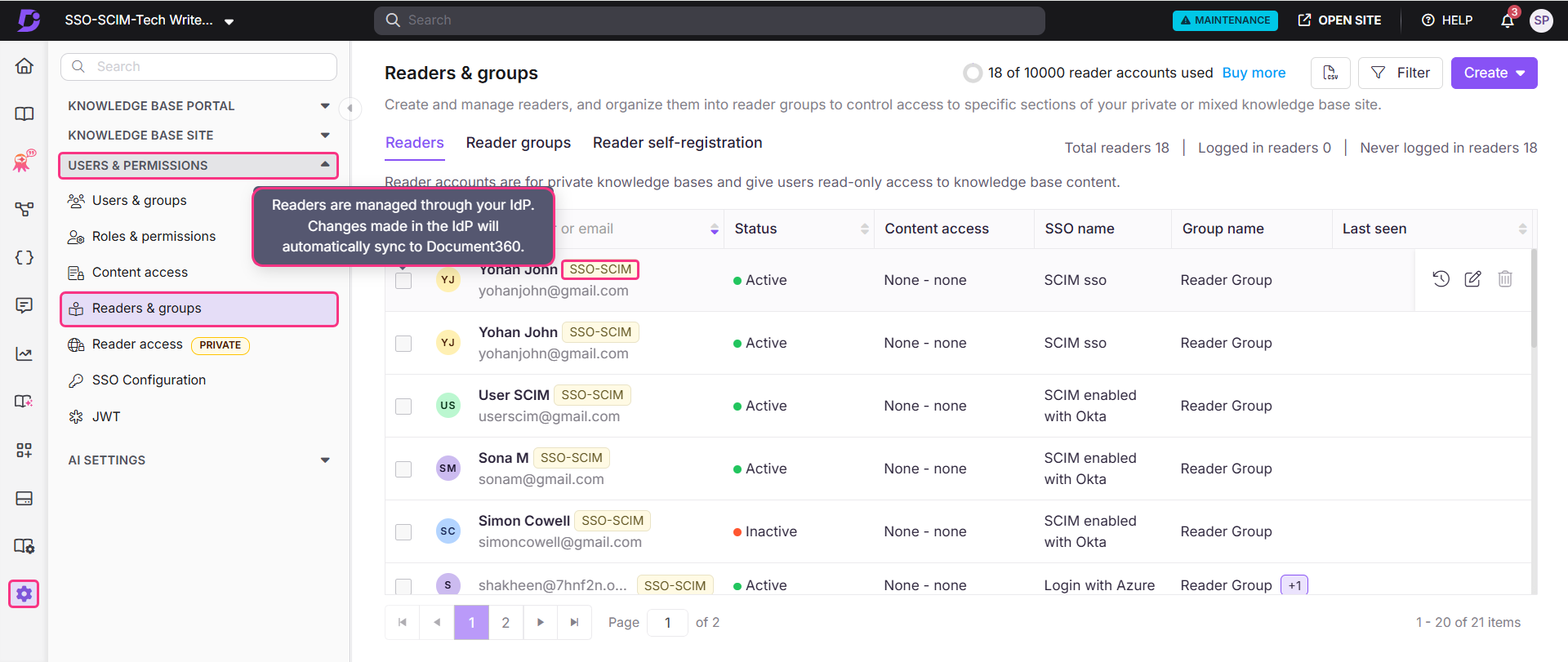
To view the readers added through your custom app,
Go to Document360 and navigate to Settings > Users & permissions > Readers & groups.
Select the reader to navigate to their reader profile.
Readers provisioned via SCIM will display an SSO-SCIM badge next to their name.
NOTE
When SCIM is enabled, editing a user's name or deleting a user directly in Document360 is disabled, as these actions must be managed through your IdP to keep both platforms in sync. You can
only manage the content access from Document360. Deleting a profile in your IdP does not remove it from Document360, the profile will remain with an Inactive status.
Manage content access of Readers, Users and Groups
The default content role assigned to any new user, reader, or group is based on what was configured during SCIM provisioning setup. Permissions will be set to None by default but can be updated at any time.
To manage content access, select the desired reader and click Manage Content Access.
Choose the desired access level from the dropdown and click Update.
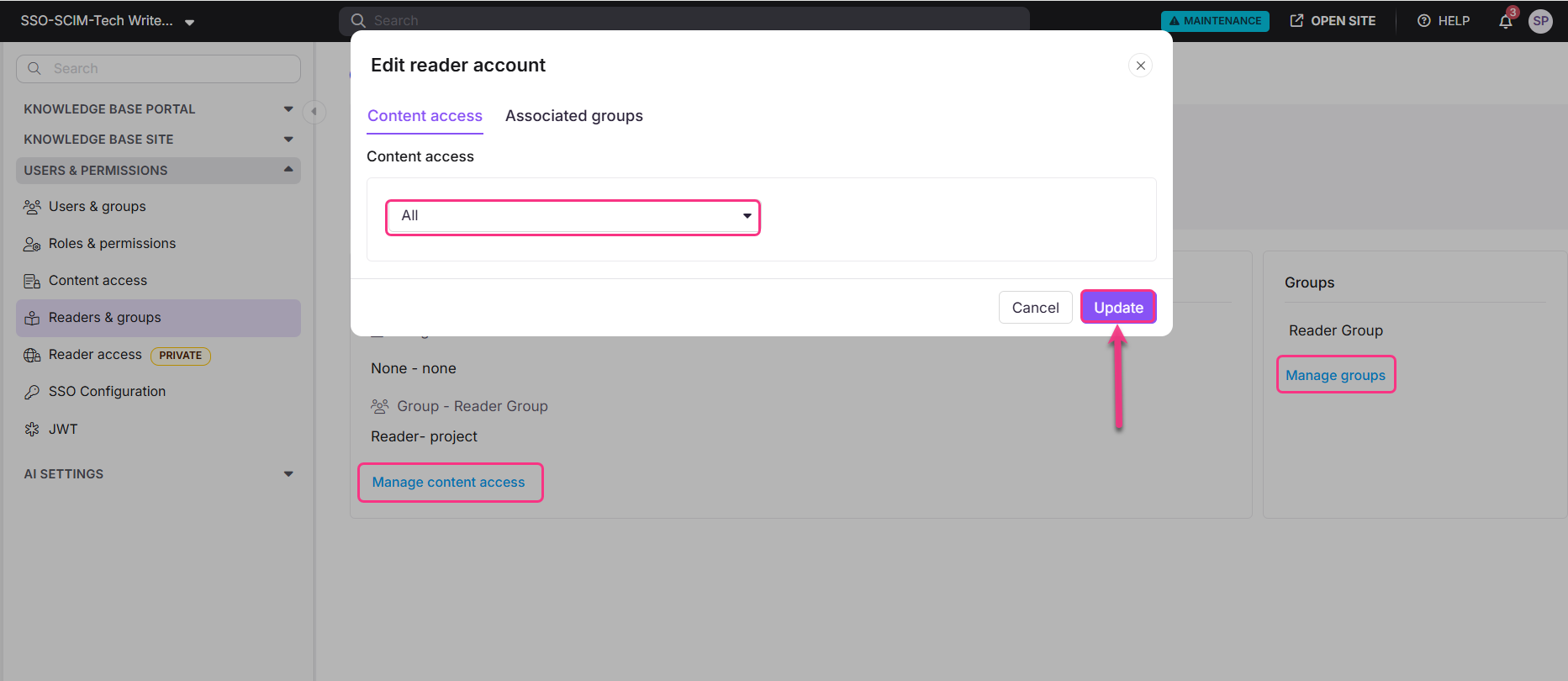
NOTE
You can also manage groups for a reader by clicking Manage groups under the Reader Group section.