Okta is an Identity Provider (IdP) that simplifies user access management by allowing users to sign in to multiple applications with a single set of credentials. This article demonstrates how to configure SSO between Okta and Document360, enabling your users to access Document360 using their Okta credentials. Please note that only users with Owner or Admin as the Project role can configure SSO in Document360.
PRO TIP
It is recommended to open Document360 and Okta in two separate tabs/browser windows, since configuring SSO in Document360 will require you to switch between Okta and Document360 multiple times.
Sign up for Okta
Access to an Okta account is a prerequisite for configuring single sign-on in Document360 with Okta. To sign up for Okta,
Navigate to https://developer.okta.com/signup/ and complete the signup process.
After signing up, you will receive an email with your login credentials and an account activation link at your registered email.
Once you click on the activation link, you will be redirected to the Okta Domain login page.
Log in with your credentials.
Once you log in, you will be redirected to the Okta developer console.
Adding an application in Okta
To create a Document360 SSO configuration using Okta, you must create a new application on Okta. To create a new application on Okta,
Log in to Okta using the credentials used while creating an Okta account.
Switch to the admin user role by clicking on Admin at the top right next to your profile name.
From the left navigation list page, expand the Applications dropdown, and click Applications.
In the Applications page, click the Create App Integration button.
In the Create a new app integration dialog, select SAML 2.0 as the Sign-in method and click Next.
Creating a SAML integration in Okta
Next, you will be redirected to the Create SAML Integration page.
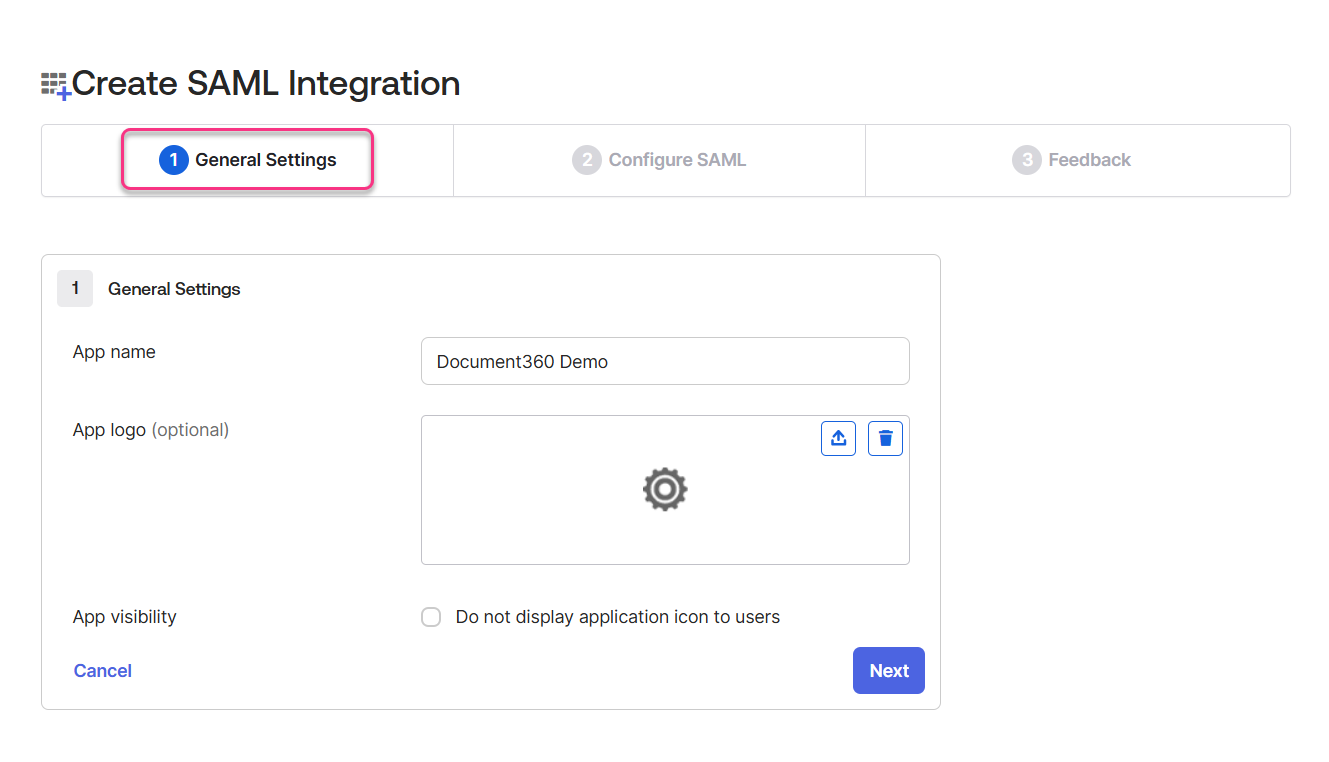
General Settings
In the General Settings tab, enter the name of your new application in the App name field.
Browse and upload a logo for your application in the Add logo field if required.
Next, you can check the App visibility checkbox if required.
Click on the Next button to navigate to the Configure SAML tab.
Configure SAML
In the Configure SAML tab, you will require the parameters provided on the Configure the Service Provider (SP) page in Document360.
To access the Configure the Service Provider (SP) page, navigate to Settings > Users & permissions > SSO Configuration in Document360.
Click the Create SSO button, select Okta in the Choose your Identity Provider (IdP) page.
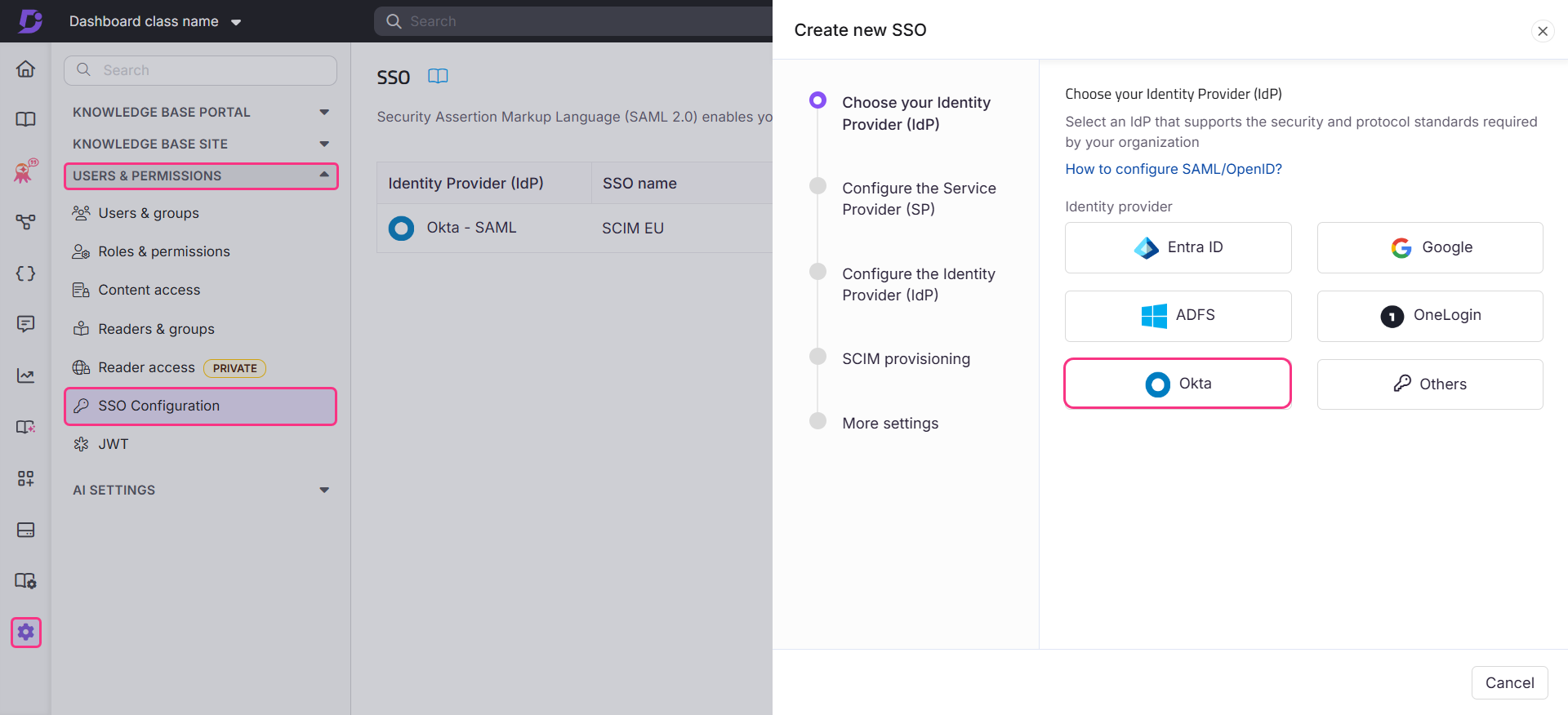
This will redirect you to the Configure the Service Provider (SP) page, which will display the parameters required to complete the SAML configuration on Okta.
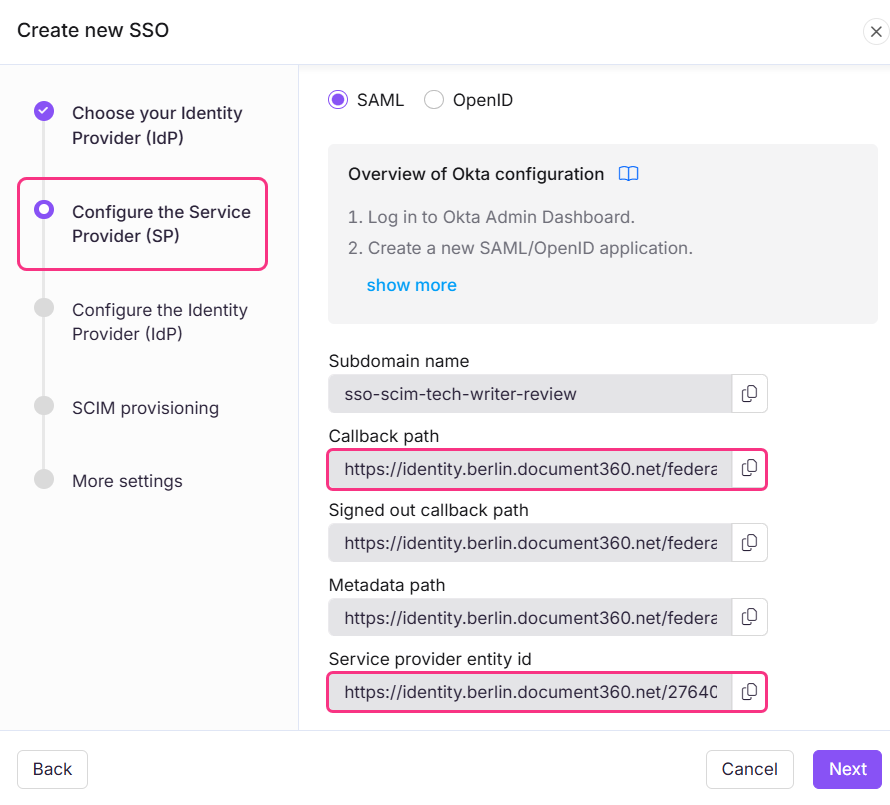
Enter the parameters from Document360 to Okta based on the below table.
Document360
Okta
Callback path
Single sign-on URL
Service provider entity id
Audience URI (SP Entity ID)
Select EmailAddress from the Name ID format dropdown menu
Select Email from the Application username dropdown menu.
NOTE
Email and name parameters are case sensitive.
.png)
Click Next to navigate to the Feedback page.
Feedback
The feedback page is for providing information to Okta about how you configure the application. Select the This is an internal app that we have created checkbox and click Finish.
.png)
You have now successfully created and configured an application in Okta with Document360.
Assign Profile attribute statements
Navigate to Sign On tab, and scroll down to Attribute statements.
Expand the Show legacy configuration and click Edit on Profile attribute statements.
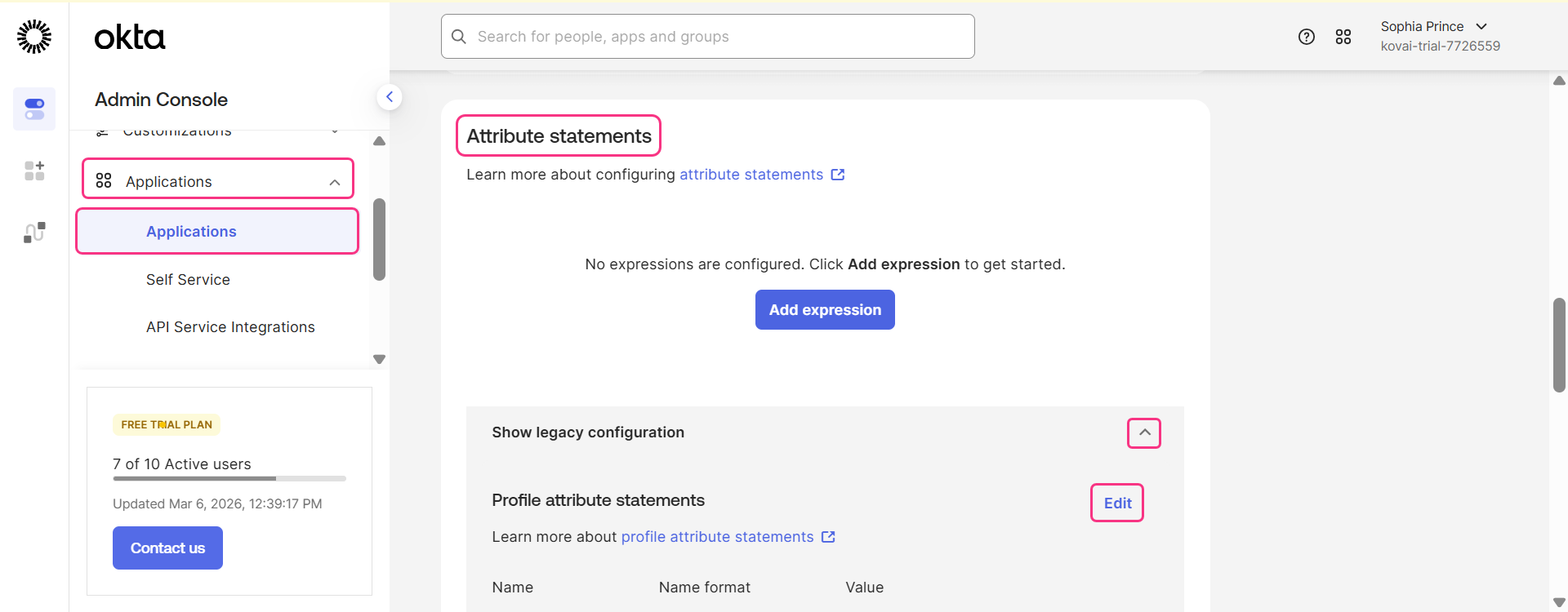
Update the necessary fields according to the table below. You will have to add two additional rows to enter all the details from the table below.
Name | Name format | Value |
|---|---|---|
urn:oasis:names:tc:SAML:2.0:nameid | URI Reference | user.email |
name | Unspecified | user.email |
Unspecified | user.email |
Click Save.
Document360 to Okta SAML SSO configuration
SAML setup instructions on Okta
On the Okta dashboard, click on the Applications dropdown and select Applications.
On the Applications page, select the active application you want to configure on Document360.
Click the Sign On tab.
Click the View SAML setup instructions button
The parameters needed to be configured will open in a new webpage.
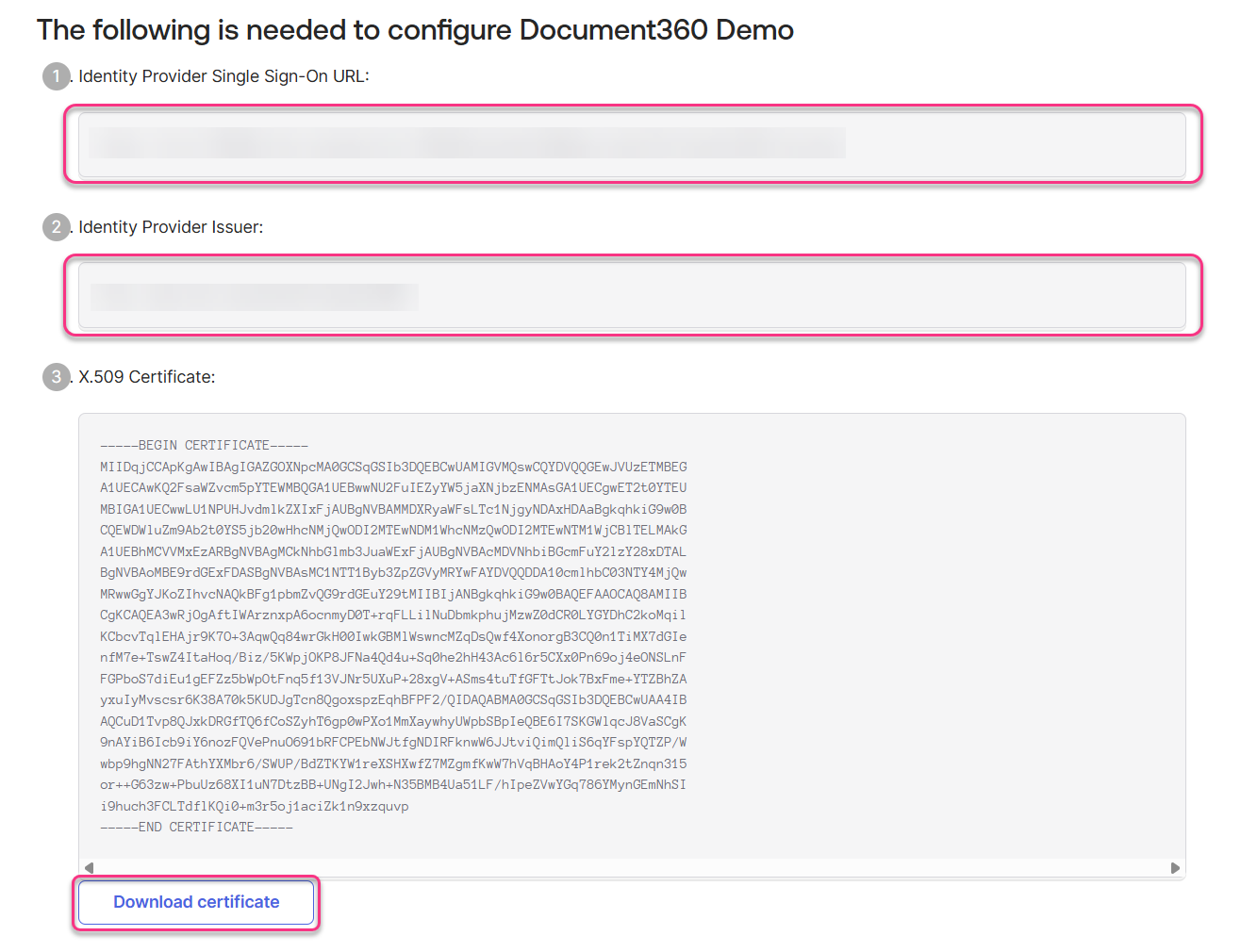
SSO configuration on Document360
Switch to the Document360 page you had opened, displaying the Configure the Service Provider (SP) page.
In Configure an existing connection field, you can inherit from an already created SSO configuration that has SCIM enabled in the parent project. By selecting and inheriting this connection, the current SSO configuration will be set as the child inherited SSO configuration and will automatically inherit the SCIM configuration from the parent.
NOTE
For more information on inheritance, go to Managing Users and Readers with SCIM in Okta
Complete the fields in the Configure the Identity Provider (IdP) page using the setup instructions from Okta.
Download the X.509 Certificate from Okta and attach the downloaded okta_cert file in the SAML certificate field on Document360.
Document360
Okta
Sign on URL
Identity Provider Single Sign-On URL
Entity ID
Identity Provider Issuer
SAML certificate
X.509 Certificate
Next, turn on/off the Allow IdP initiated sign in toggle as per your project requirements.
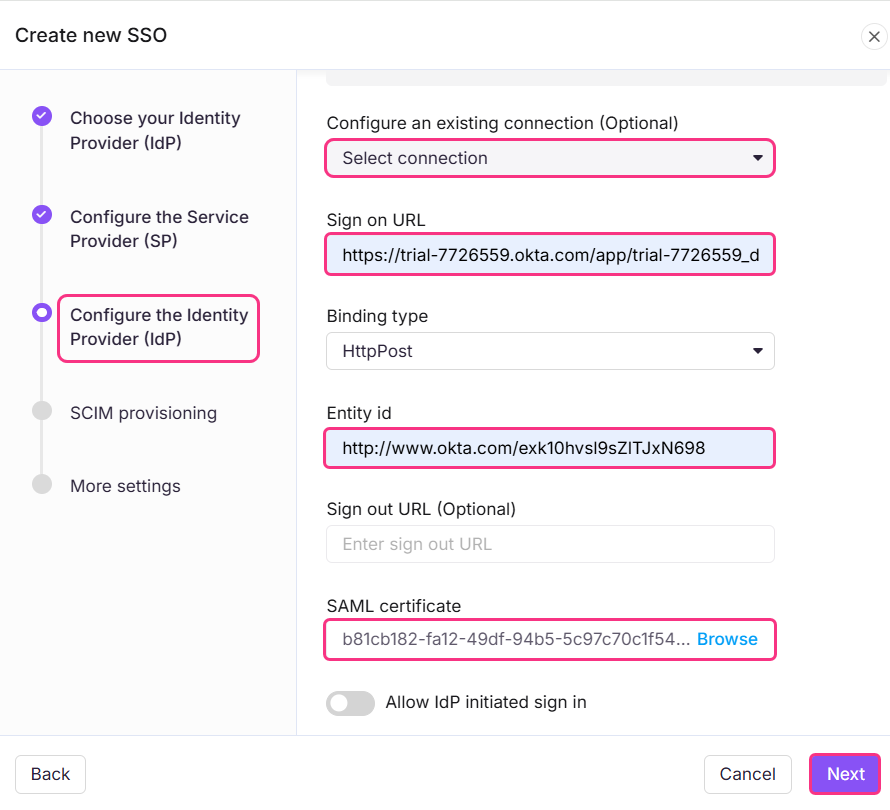
Once done, click the Next button to navigate to the SCIM provisioning page.
SCIM Provisioning with Okta
If SCIM provisioning is required,
Turn on the Enable SCIM Provisioning toggle.
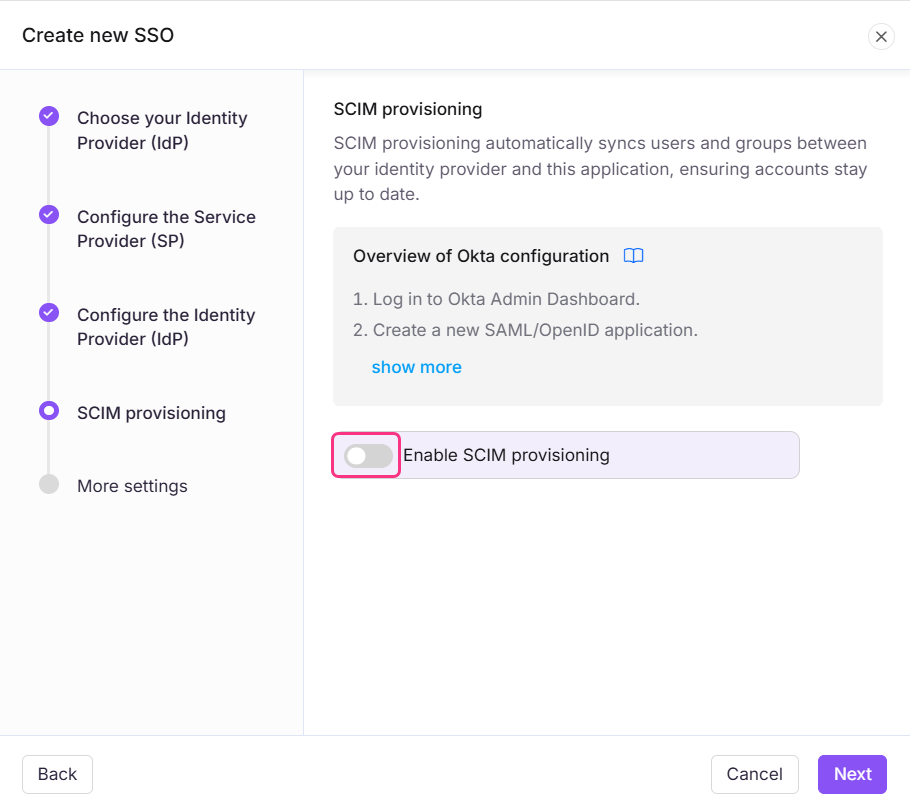
A confirmation dialog will appear outlining the terms for enabling SCIM. Review the terms, select the checkbox, and click Agree.
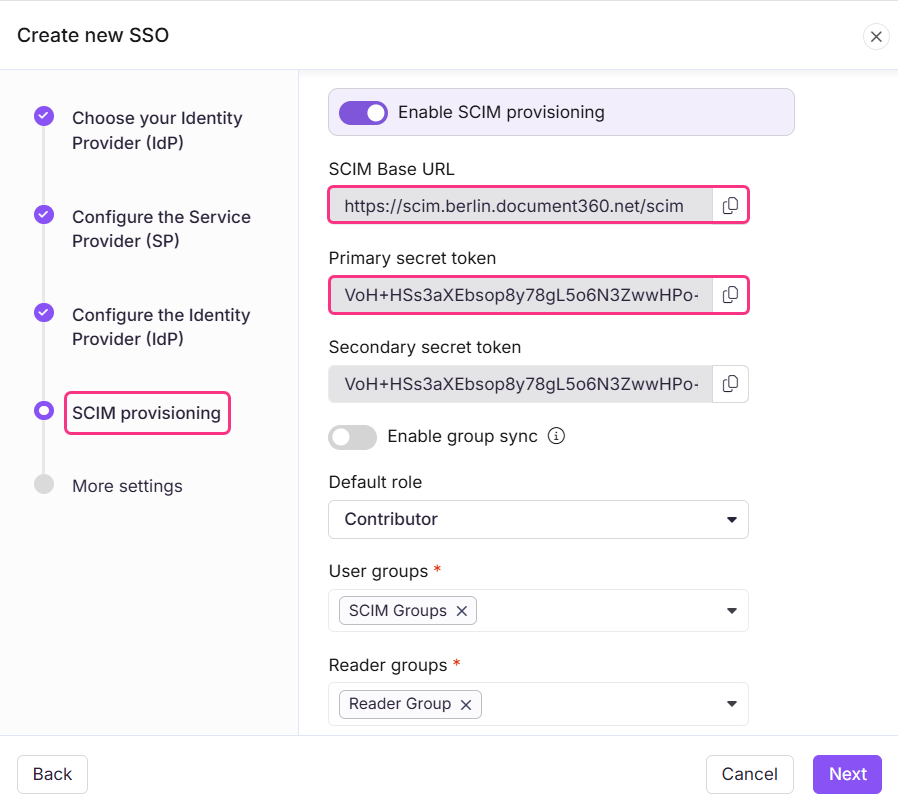
The parameters required to complete the SCIM configuration in Okta will then be displayed.
Navigate to Okta to enable SCIM provisioning
In the Okta Admin Console, expand the Applications dropdown from the left navigation bar and click Applications.
Select the application where you want to enable SCIM provisioning.
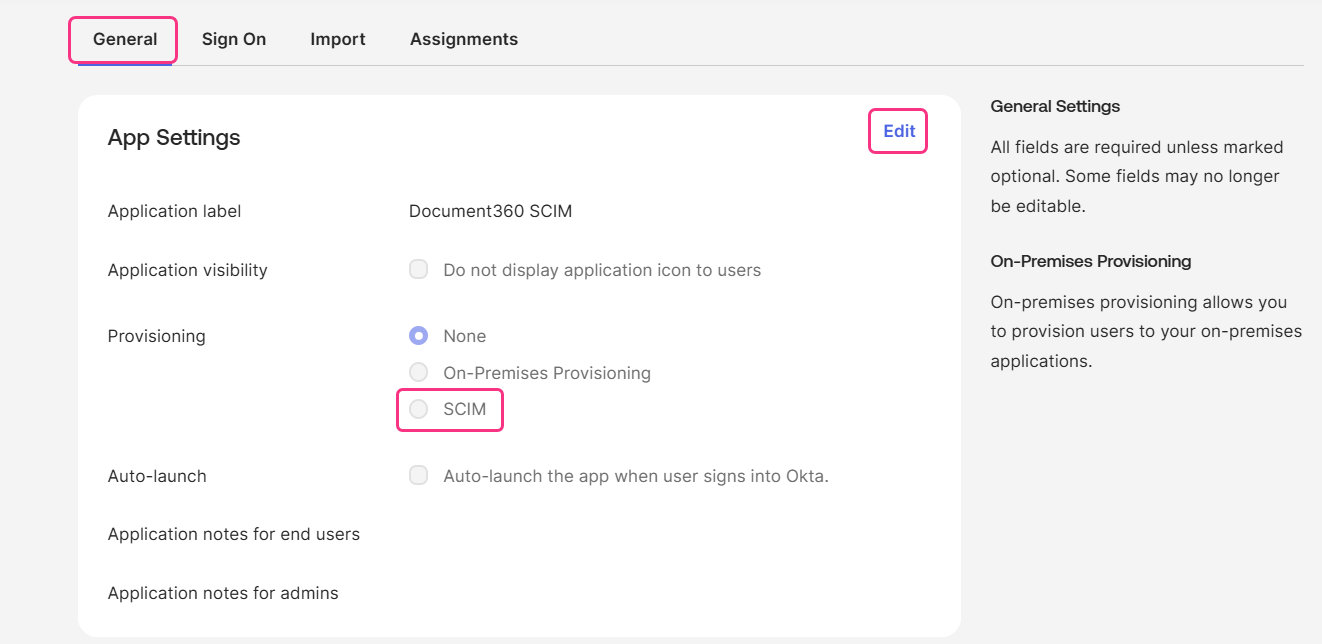
Navigate to the General tab and click Edit under App Settings.
Select the SCIM Provisioning radio button and click Save.
Provision SCIM in Okta with Document360
Go to the Provisioning tab and under the SCIM Connection section, click Edit.
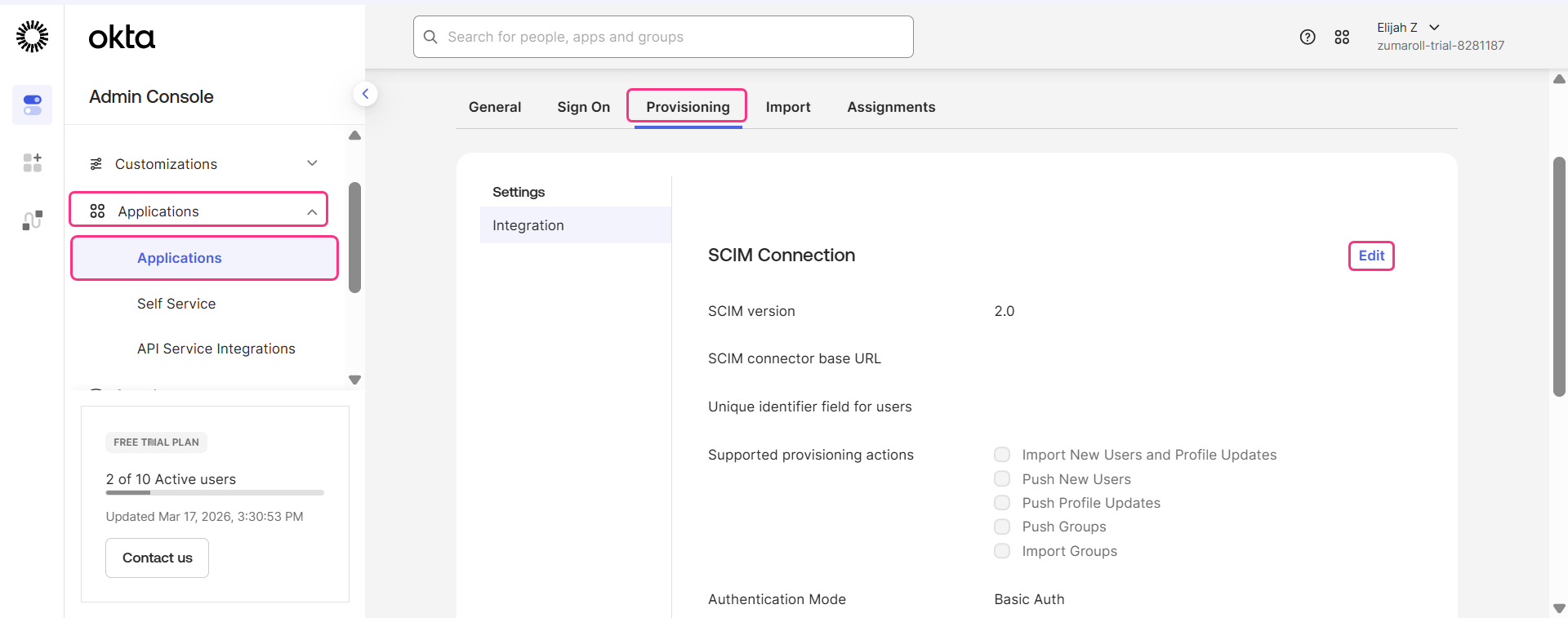
Enter the SCIM Base URL from Document360 into Okta’s SCIM connector base URL field.
Okta | Document360 |
|---|---|
SCIM connector base URL | SCIM Base URL |
HTTP Header Authorization | Primary secret token |
In the Unique identifier field for users, enter userName.
Under Supported provisioning actions, select only the options supported by Document360:
Push New Users
Push Profile Updates
Push Groups
From the Authentication mode dropdown, choose HTTP Header.
Go to Document360, and in the SCIM provisioning page, copy the Primary secret token.
Paste the Primary secret token into the HTTP Header Authorization field.
NOTE
The primary and secondary tokens are generated once and displayed only at the time of creation. You can choose to copy the primary or the secondary secret token. Ensure you copy and store them in a secure location before saving the configuration. Once the SSO configuration is saved, the tokens will appear masked when you return to edit it and cannot be retrieved. To obtain a new token, you must regenerate it. Regenerating a token invalidates the existing one, you will need to update the new token in your Okta configuration to continue syncing without interruption.
.png)
NOTE
Do not click Test Connector Configuration yet. At this stage, SCIM provisioning will not work with Document360 as the SSO configuration set up in Document360 is not completed.
Navigate to Document360 to assign default role
Go to the SCIM provisioning page in Document360 and turn on the Enable group sync toggle if required. This automatically assigns users and readers based on your IdP group mappings.
In the Default role field, the role is set to Contributor by default. You can change this from the dropdown if needed.
In the User groups and Reader groups fields, select the groups you want to add. Multiple groups can be added, and they will inherit the default role you selected earlier.
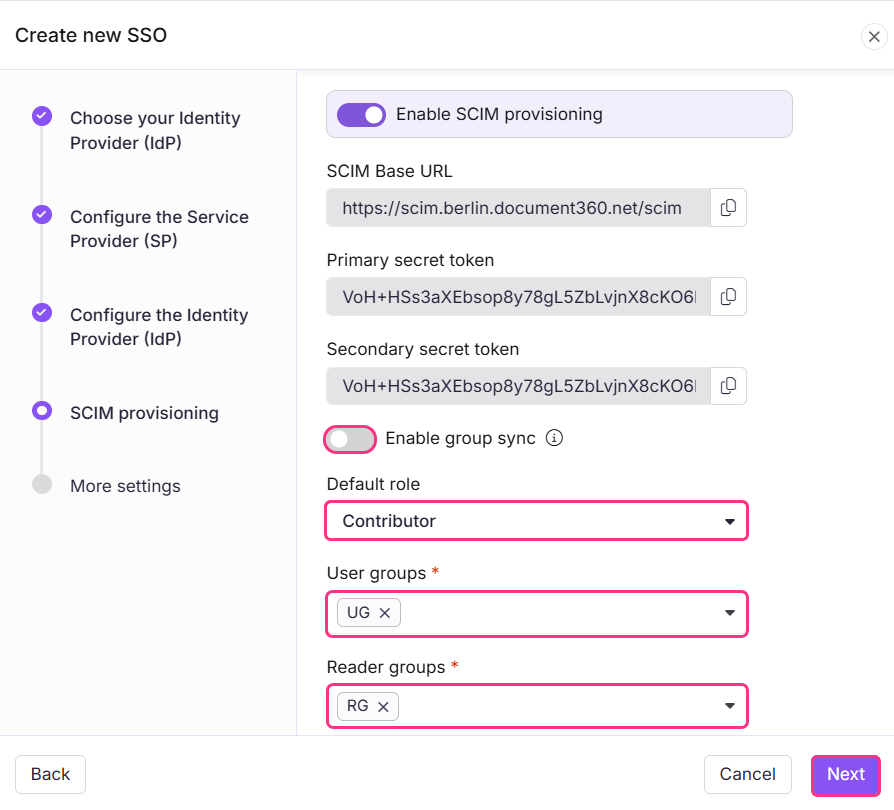
Click Next to navigate to the More settings page.
More settings
To customize SSO settings, follow the steps below,
In the More settings page, enter a name for your SSO configuration in the SSO name field.
Enter the text you want displayed on the login button in the Customize login button text field.
Enable Sign out idle SSO user if needed, and set the duration after which an idle SSO user will be automatically logged out.
Choose whether to invite all users or selected users using the Convert existing team and reader accounts to SSO radio buttons.
.png)
Click Create to complete the SSO configuration setup.
Navigate to Okta to complete SCIM provisioning with Document360
After the SSO configuration has been successfully created in Document360, SCIM provisioning can now be completed in Okta.
Navigate back to Okta Admin Console, ensure all the necessary details have been filled.
.png)
Then, click Test Connector Configuration to verify the connection between Okta and Document360.
A confirmation dialog will appear, indicating that the test was successful.
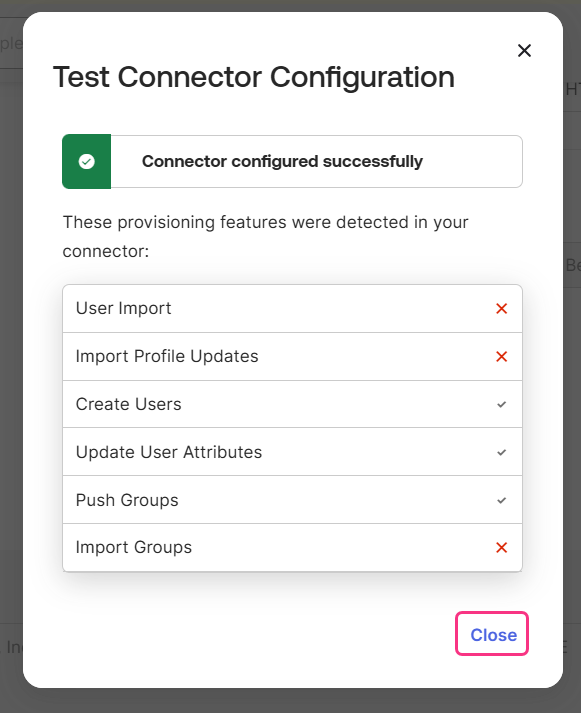
Click Save to finalize the configuration.
NOTE
For further details on how to add User, Readers, and User and Reader groups, go to Managing Users and Groups with SCIM in Okta.
The SSO configuration based on the SAML protocol has been configured using Okta successfully.
FAQ
What is the purpose of having both a primary and secondary secret token?
Having both a primary and secondary token allows you to rotate tokens safely without disrupting your SCIM integration.
For example, if your primary token is accidentally exposed in a log file or configuration, you do not need to revoke it immediately and risk breaking your user sync. Instead, you can switch your Okta integration to use the secondary token first, and then regenerate the primary token in the background. This ensures that user provisioning continues without any interruption while the compromised token is being replaced.