SCIM (System for Cross-domain Identity Management) is an open standard protocol that automates user provisioning and deprovisioning between identity providers and applications. When integrated with Microsoft Entra, SCIM allows you to automatically sync users, readers, and groups from Entra to Document360, eliminating the need for manual user management. Any changes made in Entra, such as adding, updating, or deactivating users are automatically reflected in Document360, ensuring your team always has the right level of access.
Before you begin, ensure the following prerequisites are completed:
Complete the SCIM setup in Microsoft Entra ID. For setup instructions, see SAML SSO with Entra.
Your Microsoft Entra ID application must be created as a Non-Gallery app using:
New application > Create your own application > Integrate any other application you don't find in the gallery.
If you use a Gallery app, SCIM provisioning will not be available. See SAML SSO with Entra for more details.
SAML SSO must be fully configured and working between Microsoft Entra ID and Document360.
SCIM provisioning must be enabled in Document360. Navigate to Settings > Users & permissions > SSO Configuration, open your SSO setup, and confirm the Enable SCIM provisioning toggle is turned on.
Start Provisioning
To start provisioning in Entra, ensure you have already created and integrated SCIM with Entra. Once done:
Navigate to your SCIM application in Entra and click Start provisioning.
In the confirmation dialog, click Yes.
.png)
With SCIM, you can manage readers, users, and groups, and any changes made will be automatically synced to Document360.
Assign attribute mapping
To create a new attribute mapping for the User role condition,
Open Enterprise app tab and select your SCIM SSO application.
Navigate to the Provisioning tab, then select Attribute mapping (Preview) from the left menu and click Provision Microsoft Entra ID Users.
Scroll down to the Attribute mappings section, select the Show advanced options checkbox and then click Edit attribute list for customappsso to proceed.
On the Edit attribute list page, scroll down, enter the URL parameter in the Name field, and set the Type to Boolean from the dropdown, as shown below.
Name | Type |
|---|---|
urn:ietf:params:scim:schemas:extension:document360:2.0:User:isTeamAccount | Boolean |
.png)
NOTE
Ensure there are no whitespaces when entering the URL parameter in the Name field.
Click Save, then click Yes in the confirmation dialog.
Using Expression builder to map roles
You can configure an attribute mapping expression in Entra that evaluates each user's existing profile attribute, such as Job Title, and automatically determines whether they should be provisioned as a User or a Reader in Document360.
The expression maps directly to the isTeamAccount attribute:
isTeamAccount=True→ provisioned as a UserisTeamAccount=False→ provisioned as a Reader
Steps to configure
Open your SCIM SSO application in Entra and navigate to Provisioning > Attribute Mappings.
Locate the
isTeamAccountattribute and click the Edit icon next to it. This will navigate to the Edit Attribute page.Set the Mapping type to Expression.
Enter your expression in the expression field. The expression evaluates each user's profile attribute and determines whether they should be provisioned as a User or a Reader. Refer to the Use the expression builder link below the expression field to visually build and test your expression against a real user in your directory before applying it.
NOTE
For more information on building and testing expressions in Entra, refer to Microsoft's Expression Builder documentation.
Set the Default value if null (optional) to False, this ensures that any user without a matching attribute value is provisioned as a Reader by default.
Click Ok to save the attribute.
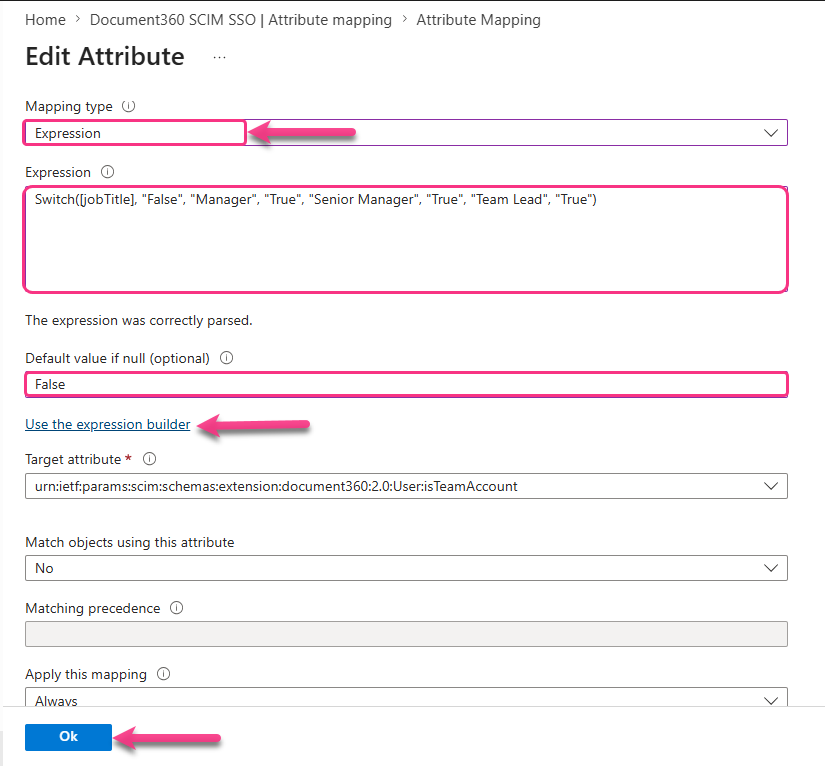
Example
If your users have a Job Title attribute in their Entra profile, you can map roles based on their title:
Switch([jobTitle], "False", "Manager", "True", "Senior Manager", "True", "Team Lead", "True")Users with the title Manager, Senior Manager, or Team Lead are provisioned as Users. Any other Job Title returns False and the user is provisioned as a Reader.
Create User, Reader & Group
Create Reader
To create a new Reader in Entra,
Expand the Entra ID dropdown in the left navigation bar and click Users.
Click New user > Create new user and fill in the required user details.
Click Create + review, then click Create to finalize and create the Reader.
.png)
Once the user is created and provisioned, Document360 automatically determines their role based on the expression configured in the Expression Builder and provisions them accordingly as a Reader.
Assign Reader to application
Once the user/reader has been created, you can assign them to desired application.
Click Enterprise apps in the left navigation bar and locate your SCIM SSO application.
Select the application and navigate to the Users and groups tab, then click Add user/group.
On the Add assignments page, click Users and groups, search for the user in the search bar, then click Select > Assign. The user has been successfully assigned to the application.
.gif)
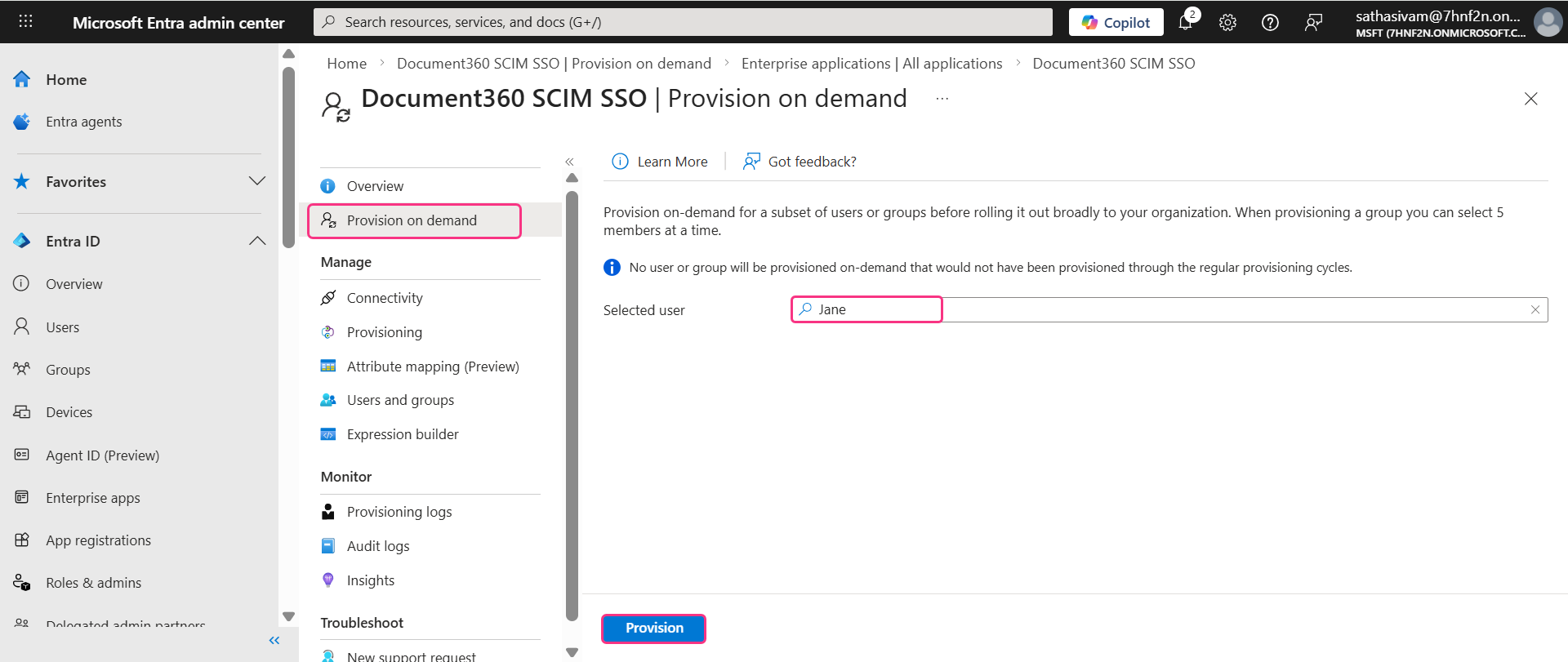
To push the user to Document360, navigate to the Provisioning tab in the left menu and click Provision on demand.
In the Selected user search bar, search for and select the user, then click Provision.
.png)
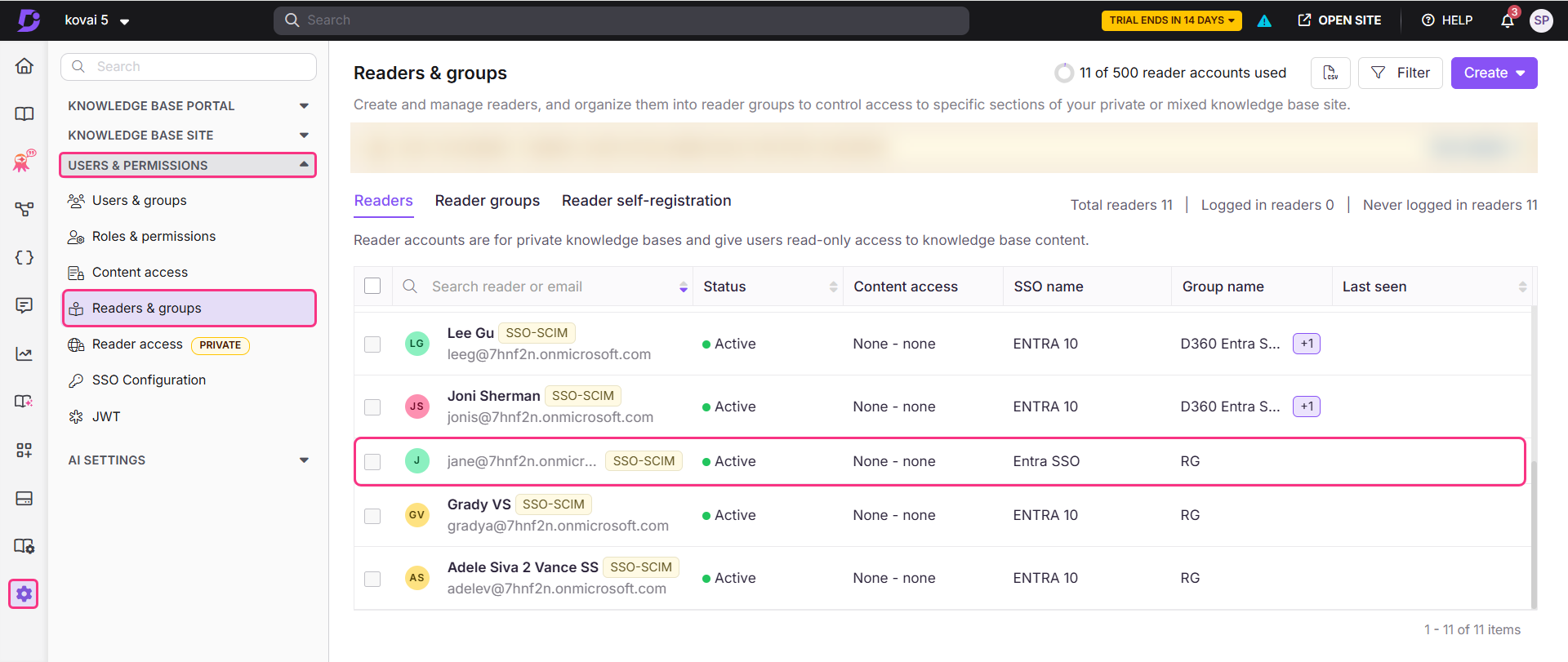
The reader will be automatically added to Document360. To verify, go to Document360 and navigate to Settings > Users & permissions > Readers & groups.
Create User
To create a new User,
Expand the Entra ID dropdown in the left navigation bar and click Users.
Click New user > Create new user and fill in the required user details.
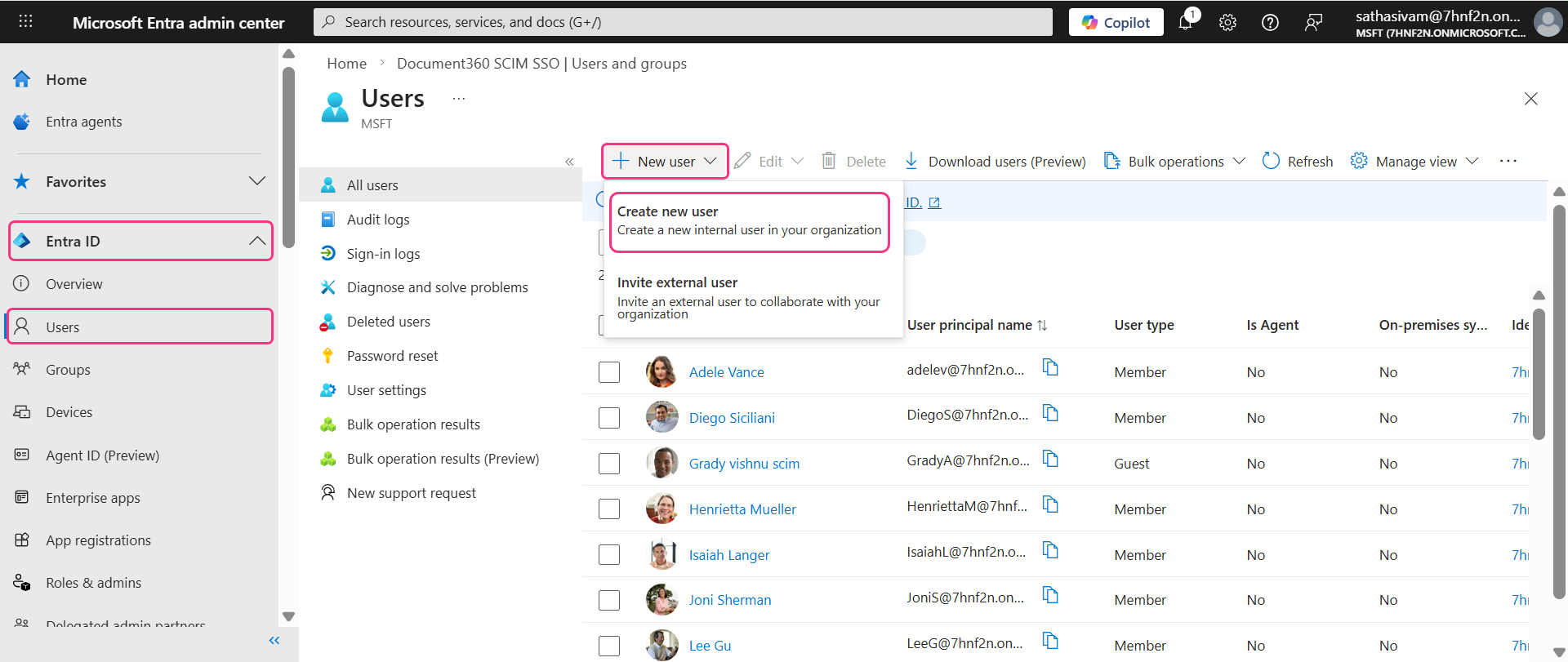
Click Create + review, then click Create to finalize and create the User.
Once the user is created and provisioned, Document360 automatically determines their role based on the expression configured in the Expression Builder and provisions them accordingly as a User.
Assign User to application
Once the user/reader has been created, you can assign them to desired application.
Click Enterprise apps in the left navigation bar and locate your SCIM SSO application.
Select the application and navigate to the Users and groups tab, then click Add user/group.
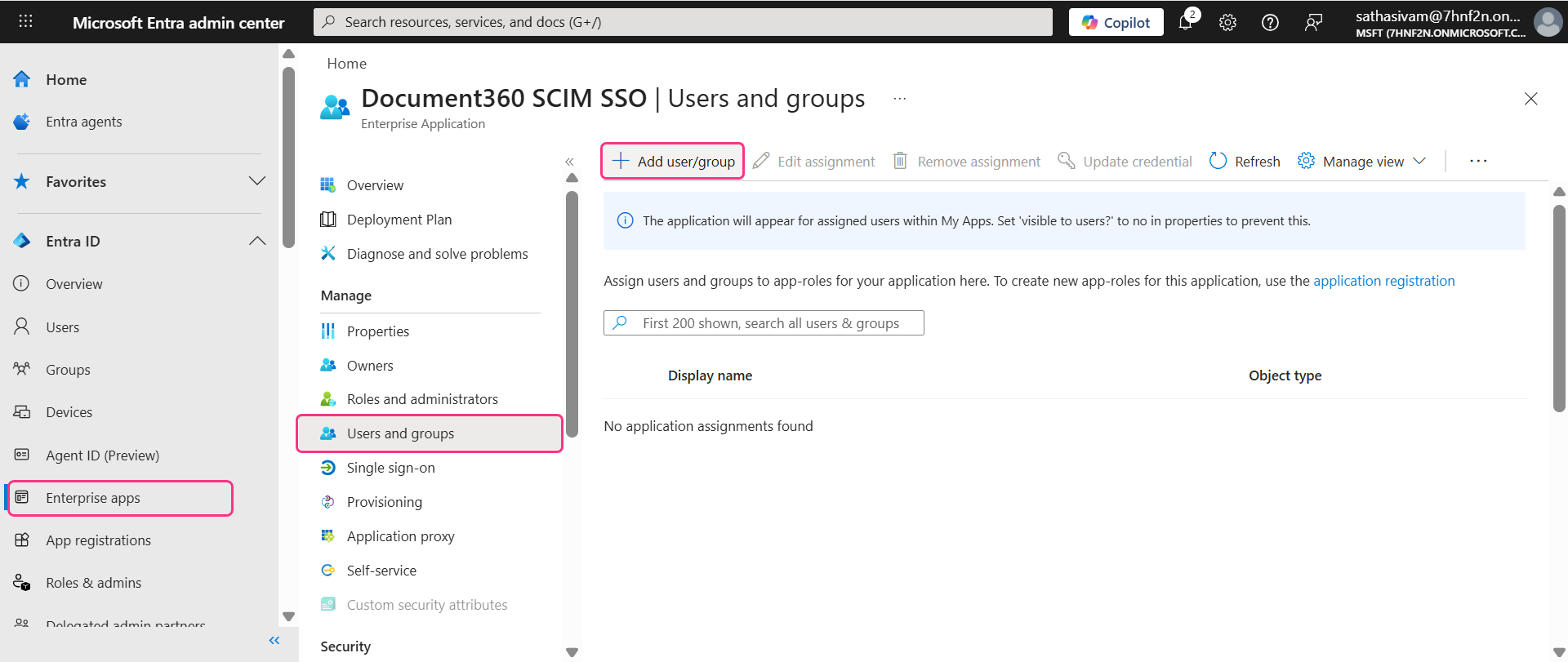
On the Add assignments page, click Users and groups, search for the user in the search bar, then click Select > Assign. The user has been successfully assigned to the application.
To push the user to Document360, navigate to the Provisioning tab in the left menu and click Provision on demand.
In the Selected user search bar, search for and select the user, then click Provision.
The user will be automatically added to Document360. To verify, go to Document360 and navigate to Settings > Users & permissions > Readers & groups.
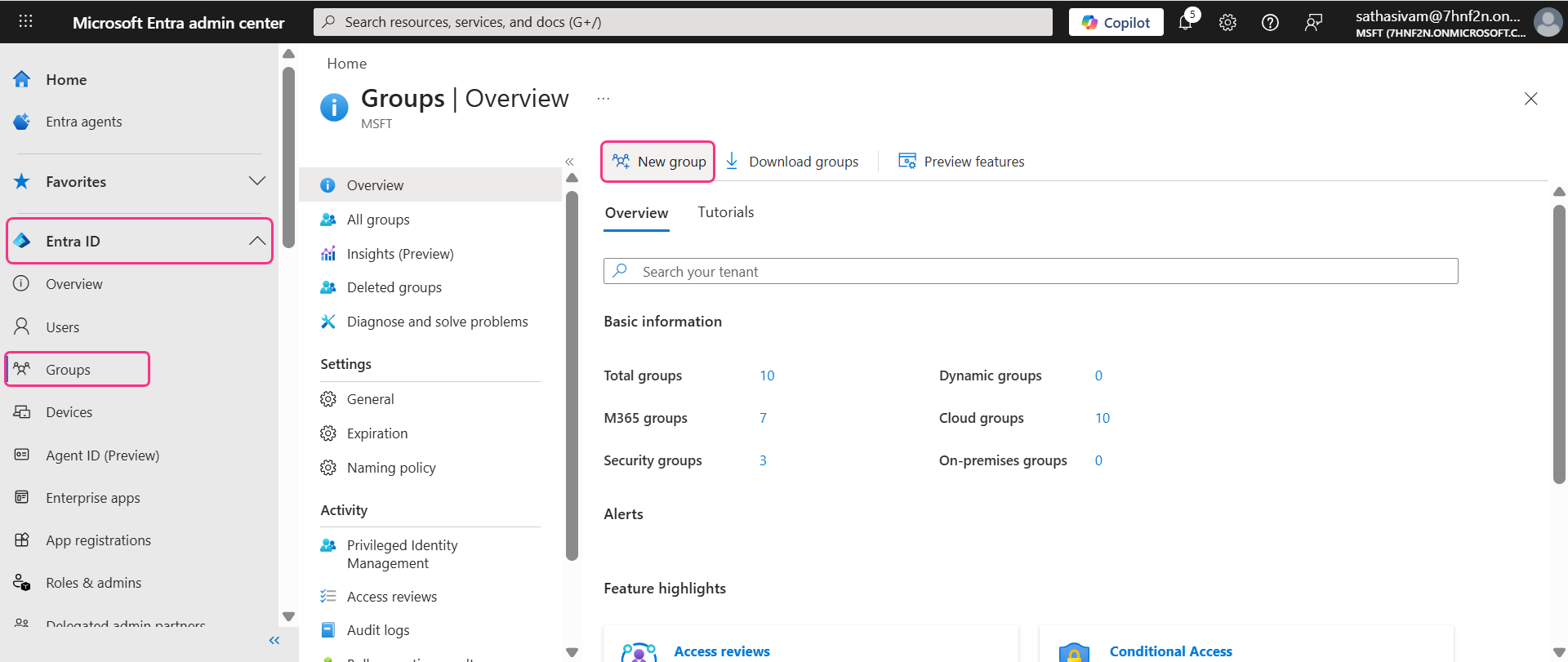
Create group
To create a new group in Entra:
Open the Groups tab in the left menu and click New Group.
Fill in the required details and click Create.
Assign Group to application
Navigate to Enterprise apps and select your SCIM SSO application.
Open the Users and groups tab, click Add user/group, then click None selected under Users and groups and search for the group name.
Select the group and click Assign.
.gif)
To provision the group to Document360:
Navigate to the Provisioning on demand tab, search for the group name, and click Provision.
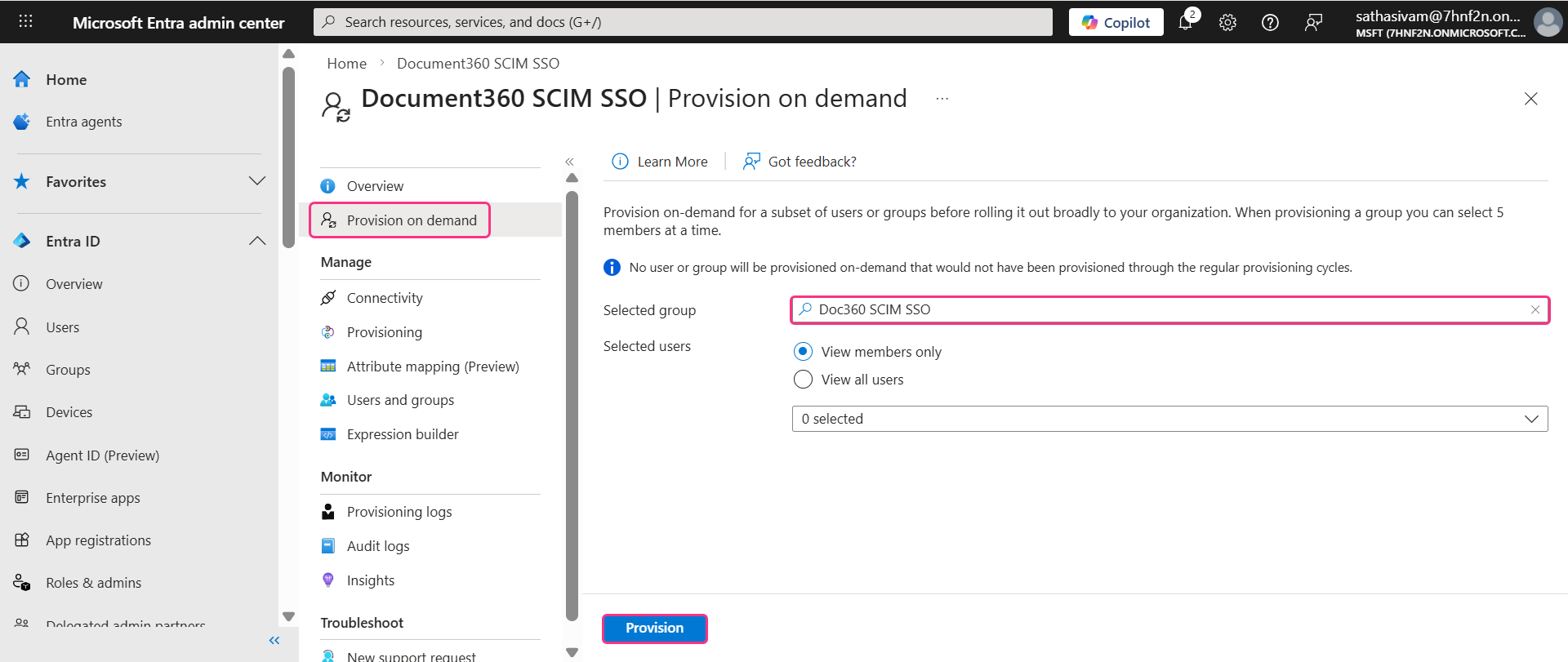
You can select the number of users or members in the group by selecting the radio buttons.
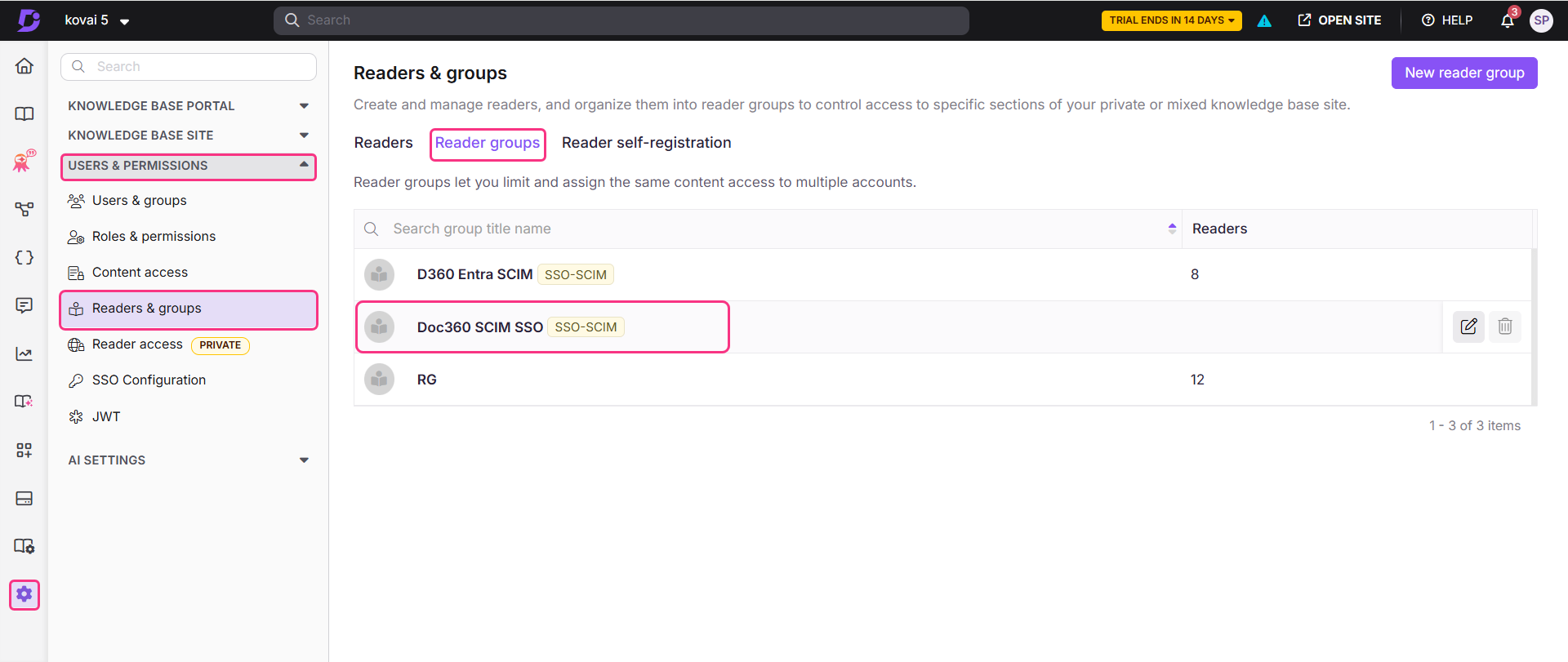
The group will be successfully added to Document360. To verify, go to Document360 and navigate to Settings > Users & permissions > Readers & groups > Reader group tab.
Manage content access for Users, Readers and groups
In Document360, user and group names cannot be edited or deleted directly, these actions must be managed from Entra. However, you can still manage roles, permissions, and content access within Document360.
Select the desired user and click Manage content access.
In the dialog, use the dropdowns to select the desired content access.
If needed, you can also manage group assignments and add the user to a desired group.
.png)
Click Update to confirm and save the changes.
Update User, Reader and Groups
To make changes to the user/group name,
In the left navigation bar, click Users and search for the user in the search bar, then click Select.
On the user's Overview page, open the Properties tab and click the Edit icon to make the necessary changes.
.png)
Once changes are made, click Save.
To reflect these changes in Document360, navigate to Enterprise apps > SCIM SSO app > Provisioning > Provision on demand.
Select the updated user in the Provisioning on demand page, then click Provision.
.png)
The updated user details will now be reflected in Document360.
Delete User, Reader or Group
To delete a user, reader or group,
Open Users tab in the left menu, and search and select the desired user.
Then, click Delete.
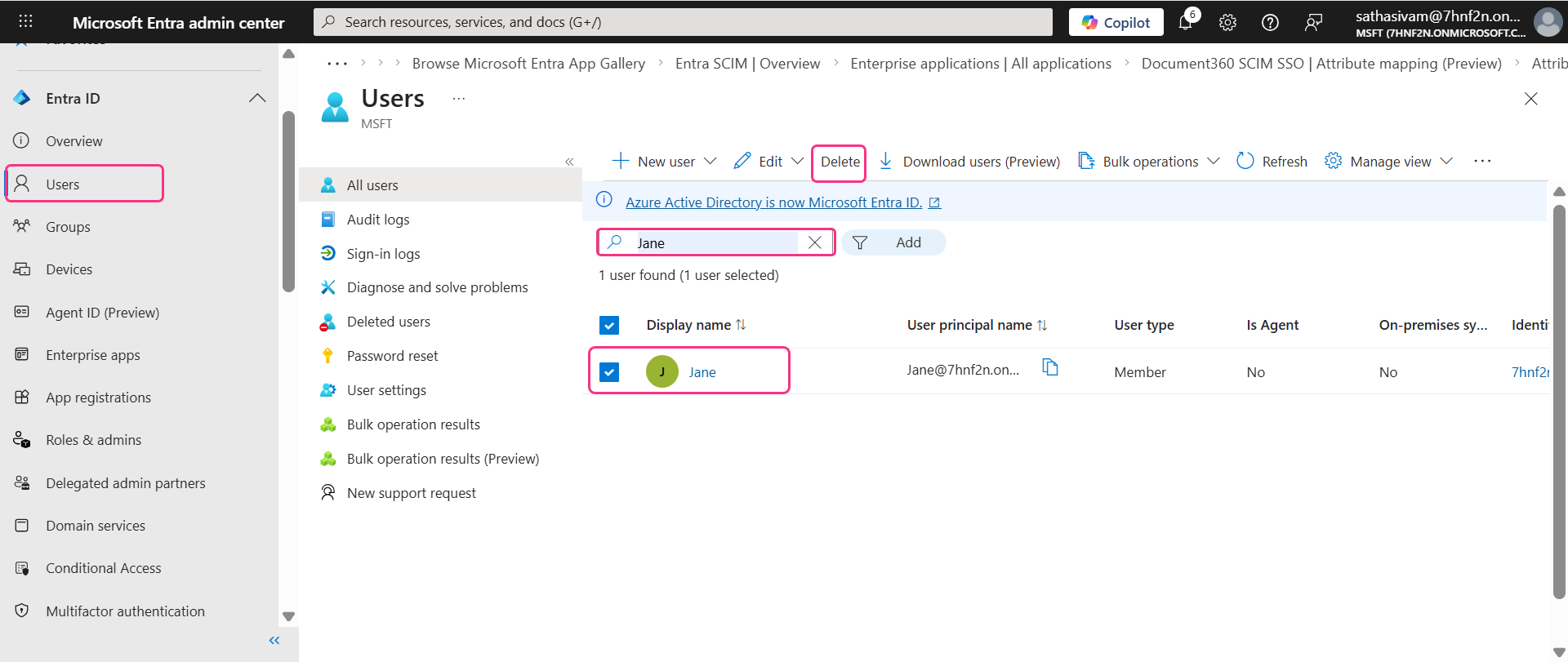
The user is deleted successfully. This change will be reflected in Document360.
NOTE
Deleting a user in Entra does not remove the user profile from Document360. Instead, the status of the user will change from Active to Inactive.
Inherit from another application
When creating a new SSO configuration in Document360, you can inherit SCIM settings from an existing SSO connection. This approach simplifies the setup process, avoids repeating configuration steps, and helps administrators save time while ensuring consistency across integrations.
Child Inherited SSO configuration
On the Configure Identity Provider (IdP) page, select the Configure an existing connection field and choose the parent SSO SCIM-enabled application you want to inherit from. Selecting this option will designate the current project as the child project, inheriting all relevant properties from the parent.
.png)
NOTE
Once the SSO configuration is created, the SCIM provisioning settings will be inherited from the parent application and cannot be modified in the child application.
Parent Inherited SSO Configuration
The parent application will display a list of all projects that have inherited its configuration. Any changes made to the parent application will automatically be reflected in the child application.
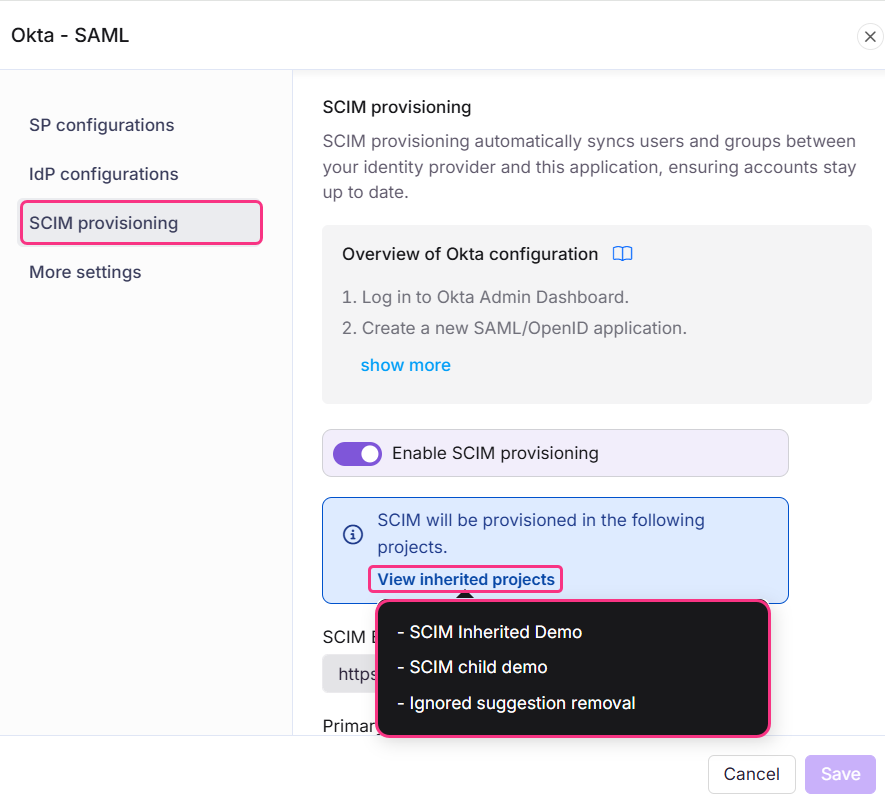
If SCIM is enabled in the parent project after child projects have already inherited it, the users and groups will be automatically provisioned to all child projects in the background.
Enabling inheritance makes it easier to manage multiple SSO configurations with SCIM enabled, as all settings are controlled from one parent application. This saves time and reduces the effort required to manage each configuration individually.
Troubleshooting
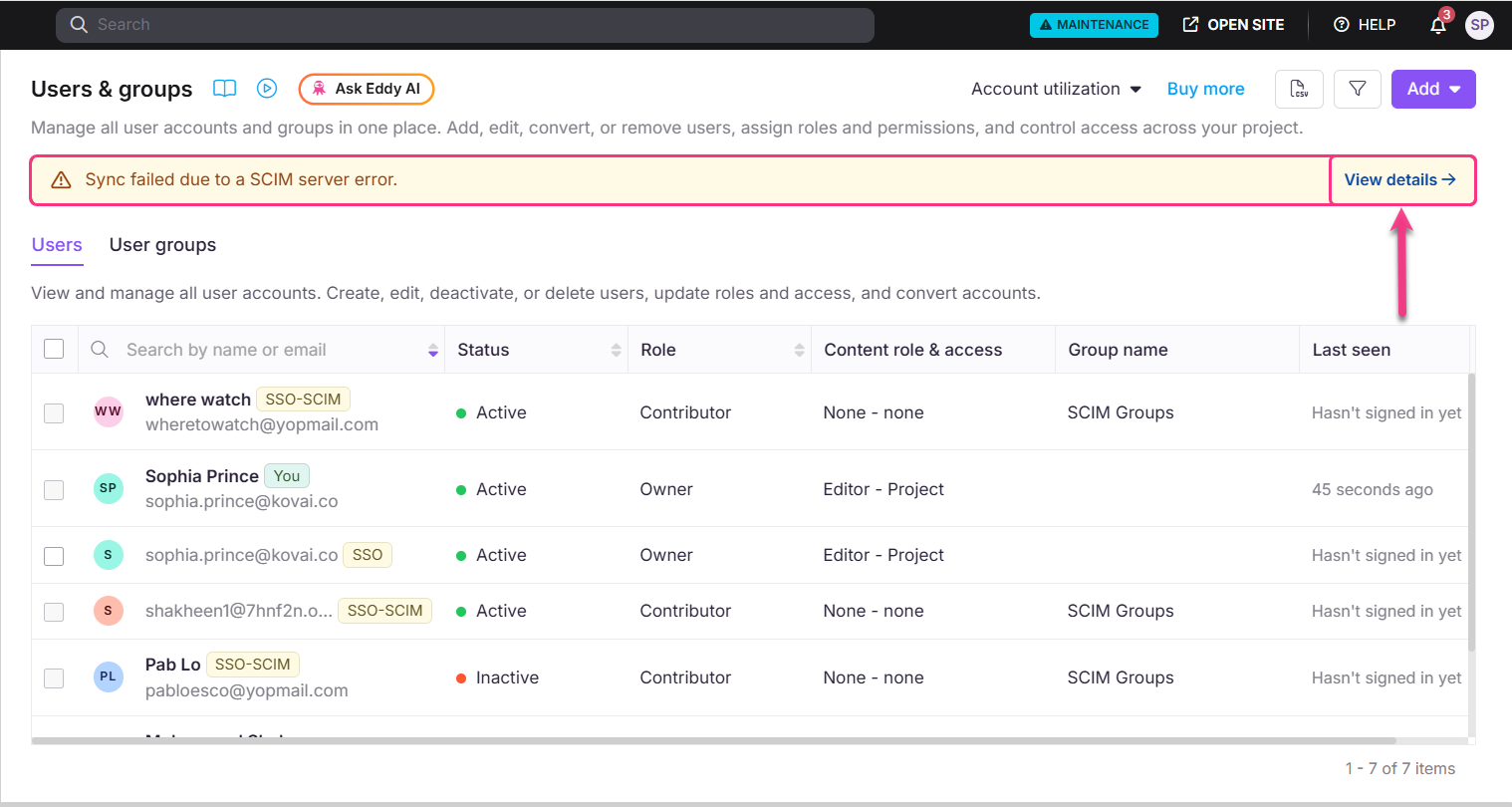
Sync failed due to a SCIM server error
When adding new users from Entra, this error indicates that one or more users could not be synced to Document360. This may be caused by:
Duplicate users provisioning
User limit reached based on your current subscription plan
Other validation or processing errors.
Click View details to see which users failed to sync.